BTS PenTesting Lab - A10 Unvalidated Redirect & Forward..
2015-12-29 09:10
344 查看
Open Redirect
源文件:/vulnerability/url/open.php
http://192.168.1.228/vulnerability/url/open.php?u=http://www.breakthesecurity.com
修改u参数就可以任意跳转,可用于钓鱼等
Open Forward
源文件:/vulnerability/url/forward.php
修改u参数就可以任意跳转,结合
<a>标签可CSRF等
File Inclusion
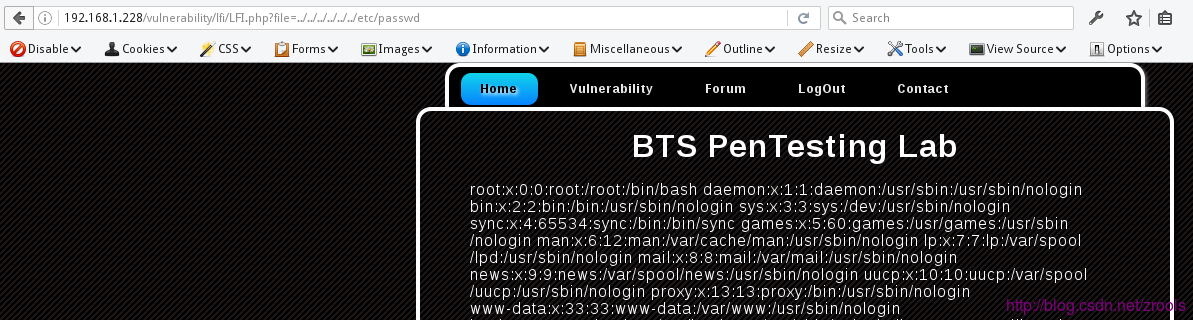
Local File Inclusion
源文件:/vulnerability/lfi/LFI.php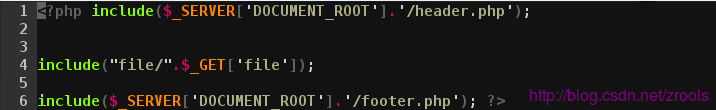
读取/etc/passwd
?file=../../../../../../etc/passwd
相关文章推荐
- BTS PenTesting Lab - A1 Injection
- BTS PenTesting Lab - A3 XSS
- BTS PenTesting Lab - A4 Insecure Direct Object References
- BTS PenTesting Lab - A5 Security Misconfiguration
- BTS PenTesting Lab - A7 Missing Function Level Access Control
- BTS PenTesting Lab - A8 CSRF
- DVWA-WooYun SQL Injection
- BTS PenTesting Lab - More..
- 【深入ASP.NET原理系列】--ASP.NET请求管道、应用程序生命周期、整体运行机制
- android Graphics( 五):drawText()详解
- shell脚本中的数学运算
- 九度OJ 1065 输出梯形 (模拟)
- Eclipse构建Maven项目
- IOS开发 @property中assign、copy 、retain等关键字的理解
- iOS Quartz 2D 绘制图形(线段\三角形\矩形\圆\圆弧等)
- 2015.12.27和2015.12.28回顾
- js实现商城星星评分的效果
- LeetCode 062 Unique Paths
- 16-《电子入门趣谈》第三章_电子世界中的五官---传感器-3.2.1DS18B20
- linux 常用命令
