asp.net 删除文件 对路径“”访问被拒绝
2013-12-10 10:16
791 查看
Application Pool Identities
By ThomasDeml
March 24, 2009
Introduction
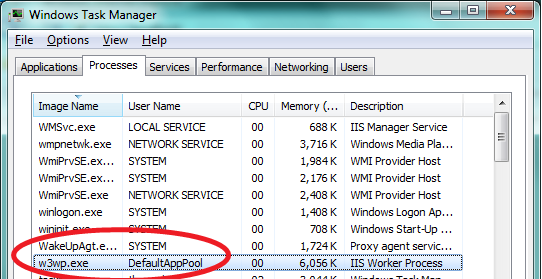
IIS introduces a new security feature in Service Pack 2 (SP2) of Windows Server 2008 and Windows Vista. It's called Application Pool Identities. Application Pool Identities allow you to run Application Pools under a unique account without having to create andmanage domain or local accounts. The name of the Application Pool account corresponds to the name of the Application Pool. The image below shows an IIS worker process (W3wp.exe) running as the DefaultAppPool identity.
Application Pool Identity Accounts
Worker processes in IIS 6.0, and in IIS 7 and above, run as NETWORKSERVICE by default. NETWORKSERVICE is a built-in Windows identity. It doesn't require a password and has only user privileges; that is, it is relatively low-privileged. Running as a low-privilegedaccount is a good security practice because then a software bug can't be used by a malicious user to take over the whole system.
However, a problem arose over time as more and more Windows system services started to run as NETWORKSERVICE. This is because services running as NETWORKSERVICE can tamper with other services that run under the same identity. Because IIS worker processes run
third-party code by default (Classic ASP, ASP.NET, PHP code), it was time to isolate IIS worker processes from other Windows system services and run IIS worker processes under unique identities. The Windows operating system provides a feature called "Virtual
Accounts" that allows IIS to create unique identities for each of its Application Pools. Click herefor
more information about Virtual Accounts.
Configuring IIS Application Pool Identities
If you are running IIS 7.5 on Windows Server 2008 R2, you don't have to do anything to use the new identity. For every Application Pool you create, the IIS Admin Process (WAS) will create a virtual account with the name of the new Application Pool and run theApplication Pool's worker processes under this account.
If you are running Windows Server 2008, you have to change the IdentityType property of the Application Pools you create to "AppPoolIdentity". Here is how:
Open the IIS Management Console (INETMGR.MSC).
Open the Application Pools node underneath the machine node. Select the Application Pool you want to change to run under an automatically generated Application Pool Identity.
Right click the Application Pool and select "Advanced Settings..."
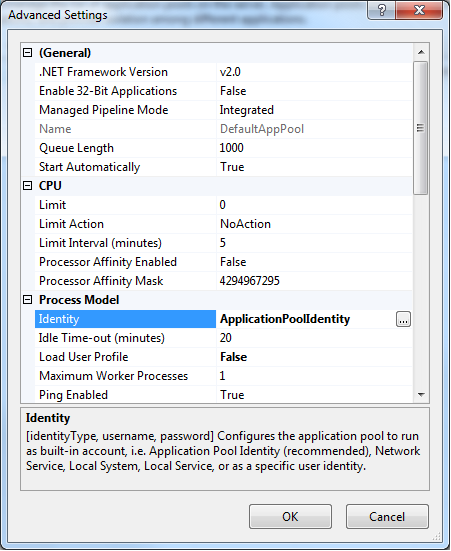
Select the "Identity" list item and click the ellipsis (the button with the three dots).
The following dialog appears.
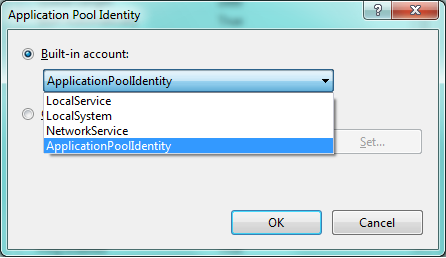
Select the Identity Type "ApplicationPoolIdentity" from the combo box.
To do the same step by using the command-line, you can call the appcmd command-line tool the following way:
%windir%\system32\inetsrv\appcmd.exe
set
AppPool
<your
AppPool>
-processModel.identityType:ApplicationPoolIdentity
Securing Resources
Whenever a new Application Pool is created, the IIS management process creates a security identifier (SID) that represents the name of the Application Pool itself. For example, if you create an Application Pool with the name "MyNewAppPool," a security identifierwith the name "MyNewAppPool" is created in the Windows Security system. From this point on, resources can be secured by using this identity. However, the identity is not a real user account; it will not show up as a user in the Windows User Management Console.
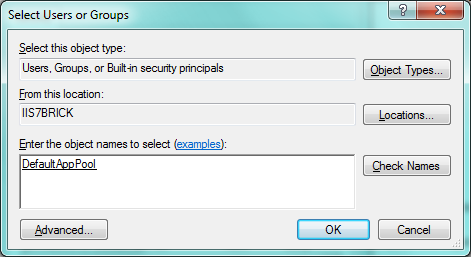
You can try this by selecting a file in Windows Explorer and adding the "DefaultAppPool" identity to the file's Access Control List (ACL).
Open Windows Explorer
Select a file or directory.
Right click the file and select "Properties"
Select the "Security" tab
Click the "Edit" and then "Add" button
Click the "Locations" button and make sure you select your machine.
Enter "IIS AppPool\DefaultAppPool" in the "Enter the object names to select:" text box.
Click the "Check Names" button and click "OK".
By doing this, the file or directory you selected will now also allow the "DefaultAppPool" identity access.
You can do this via the command-line by using the ICACLS tool. The following example gives full access to the DefaultAppPool identity.
ICACLS
test.txt
/grant
"IIS AppPool\DefaultAppPool":F
On Windows 7 and Windows Server 2008 R2, the default is to run Application Pools as the Application Pool Identity. To make this happen, a new identity type with the name "AppPoolIdentity" was introduced. If the "AppPoolIdentity" identity type is selected (the
default on Windows 7 and Windows Server 2008 R2), IIS will run worker processes as the Application Pool identity. With every other identity type, the security identifier will only be injected into the access token of the process. If the identifier is injected,
content can still be ACLed for the AppPool identity, but the owner of the token is probably not unique. Here is
an article that explains this concept.
Accessing the Network
Using the NETWORKSERVICE account in a domain environment has a great benefit. Worker process running as NETWORKSERVICE access the network as the machine account. Machine accounts are generated when a machine is joined to a domain. They look like this:<domainname>\<machinename>$,
for example:
mydomain\machine1$
The nice thing about this is that network resources like file shares or SQL Server databases can be ACLed to allow this machine account access.
WHAT ABOUT APPPOOL IDENTITIES?
The good news is that Application Pool identities also use the machine account to access network resources. No changes are required.
Compatibility Issues with Application Pool Identities
GUIDANCE DOCUMENTATION
The biggest compatibilty issue with Application Pool Identities is probably earlier guidance documents which explicitly recommend that you ACL resources for NETWORKSERVICE, that is, the default identity of the DefaultAppPool in IIS 6.0 and IIS 7.0. Customerswill have to change their scripts to ACL for "IIS AppPool\DefaultAppPool" when running on IIS 7.5 (see the example above for how to do this).
USER PROFILE
IIS doesn't load the Windows user profile, but certain applications might take advantage of it anyway to store temporary data. SQL Express is an example of an application that does this. However, a user profile has to be created to store temporary data in eitherthe profile directory or in the registry hive. The user profile for the NETWORKSERVICE account was created by the system and was always available. However, with the switch to unique Application Pool identities, no user profile is created by the system. Only
the standard Application Pools (DefaultAppPool and Classic .NET AppPool) have user profiles on disk. No user profile is created if the Administrator creates a new Application Pool.
However, if you want, you can configure IIS Application Pools to load the user profile by setting the "LoadUserProfile" attribute to "true".
Summary
Application Pool Identities are a powerful new isolation feature introduced for Windows Server 2008, Windows Vista, Windows 7 and Windows Server 2008 R2. It will make running IIS applications even more secure and reliable.
相关文章推荐
- Asp.net "对路径的访问被拒绝" 解决办法(不是文件的一部分)
- [转载]ASP.NET对路径"xxxxx"的访问被拒绝的解决方法小结
- 解决:CS0016: 未能写入输出文件 "....Framework\v4.0.30319\Temporary ASP.NET Files..."拒绝访问。
- asp.net 文件复制或删除用相对路径,File.Copy中用相对路径,巧用相对路径复制文件
- 解决:CS0016: 未能写入输出文件 "....Framework\v4.0.30319\Temporary ASP.NET Files..."拒绝访问。
- Asp.net "对路径的访问被拒绝" 解决方法的分析
- Asp.net 对路径“***”的访问被拒绝
- ASP.NET File.Delete只读文件引起的访问被拒绝,设置文件属性为Normal
- asp.net 未能写入输出文件--“拒绝访问的解决办法
- asp.net 未能写入输出文件--“拒绝访问的解决办法
- asp.net iis 对路径的访问被拒绝
- asp.net 未能写入输出文件--“拒绝访问”的解决办法
- asp.net 未能写入输出文件--“拒绝访问的解决办法
- 对路径" "的访问被拒绝XP中IIS下asp.net程序错误提示解决方案
- 对路径“C:\WINDOWS\Microsoft.NET\Framework\v1.1.4322\Temporary ASP.NET Files\aa\……”的访问被拒绝
- ASP.NET导入Excel文件,提示“拒绝访问。”解决方法。
- asp.net 上传图片时出现“对路径“D:....”的访问被拒绝
- ASP.NET IIS System.UnauthorizedAccessException: 对路径“C:\......xls”的访问被拒绝。
- ASP.NET对路径"xxxxx"的访问被拒绝的解决方法
- asp.net文件压缩,下载,物理路径,相对路径,删除文件
