poj 2635 高精度+素数
2013-03-11 16:09
197 查看
The Embarrassed Cryptographer
Description
The young and very promising cryptographer Odd Even has implemented the security module of a large system with thousands of users, which is now in use in his company. The cryptographic keys are
created from the product of two primes, and are believed to be secure because there is no known method for factoring such a product effectively.
What Odd Even did not think of, was that both factors in a key should be large, not just their product. It is now possible that some of the users of the system have weak keys. In a desperate attempt not to be fired, Odd Even secretly goes through all the users
keys, to check if they are strong enough. He uses his very poweful Atari, and is especially careful when checking his boss' key.
Input
The input consists of no more than 20 test cases. Each test case is a line with the integers 4 <= K <= 10100 and 2 <= L <= 106. K is the key itself, a product of two primes. L is the wanted minimum size of the factors in the key. The input
set is terminated by a case where K = 0 and L = 0.
Output
For each number K, if one of its factors are strictly less than the required L, your program should output "BAD p", where p is the smallest factor in K. Otherwise, it should output "GOOD". Cases should be separated by a line-break.
Sample Input
Sample Output
Source
Nordic 2005
大致题意:
给定一个大数K,K是两个大素数的乘积的值。
再给定一个int内的数L
问这两个大素数中最小的一个是否小于L,如果小于则输出这个素数。
解题思路:
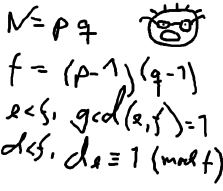
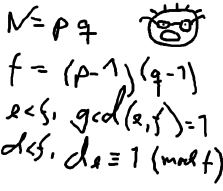
首先对题目的插图表示无语。。。
高精度求模+同余模定理
1、 Char格式读入K。把K转成千进制Kt,同时变为int型。
把数字往大进制转换能够加快运算效率。若用十进制则耗费很多时间,会TLE。
千进制的性质与十进制相似。
例如,把K=1234567890转成千进制,就变成了:Kt=[ 1][234][567][890]。
为了方便处理,我的程序是按“局部有序,全局倒序”模式存放Kt
即Kt=[890][567][234][1 ] (一个中括号代表一个数组元素)
2、 素数打表,把10^6内的素数全部预打表,在求模时则枚举到小于L为止。
注意打表不能只打到100W,要保证素数表中最大的素数必须大于10^6,否则当L=100W且K为GOOD时,会因为数组越界而RE,这是因为越界后prime都是负无穷的数,枚举的while(prime[pMin]<L)循环会陷入死循环
3、 高精度求模。
主要利用Kt数组和同余模定理。
例如要验证123是否被3整除,只需求模124%3
但当123是一个大数时,就不能直接求,只能通过同余模定理对大数“分块”间接求模
具体做法是:
先求1%3 = 1
再求(1*10+2)%3 = 0
再求 (0*10+4)% 3 = 1
那么就间接得到124%3=1,这是显然正确的
而且不难发现, (1*10+2)*10+4 = 124
这是在10进制下的做法,千进制也同理,*10改为*1000就可以了
| Time Limit: 2000MS | Memory Limit: 65536K | |
| Total Submissions: 10550 | Accepted: 2776 |
The young and very promising cryptographer Odd Even has implemented the security module of a large system with thousands of users, which is now in use in his company. The cryptographic keys are
created from the product of two primes, and are believed to be secure because there is no known method for factoring such a product effectively.
What Odd Even did not think of, was that both factors in a key should be large, not just their product. It is now possible that some of the users of the system have weak keys. In a desperate attempt not to be fired, Odd Even secretly goes through all the users
keys, to check if they are strong enough. He uses his very poweful Atari, and is especially careful when checking his boss' key.
Input
The input consists of no more than 20 test cases. Each test case is a line with the integers 4 <= K <= 10100 and 2 <= L <= 106. K is the key itself, a product of two primes. L is the wanted minimum size of the factors in the key. The input
set is terminated by a case where K = 0 and L = 0.
Output
For each number K, if one of its factors are strictly less than the required L, your program should output "BAD p", where p is the smallest factor in K. Otherwise, it should output "GOOD". Cases should be separated by a line-break.
Sample Input
143 10 143 20 667 20 667 30 2573 30 2573 40 0 0
Sample Output
GOOD BAD 11 GOOD BAD 23 GOOD BAD 31
Source
Nordic 2005
大致题意:
给定一个大数K,K是两个大素数的乘积的值。
再给定一个int内的数L
问这两个大素数中最小的一个是否小于L,如果小于则输出这个素数。
解题思路:
首先对题目的插图表示无语。。。
高精度求模+同余模定理
1、 Char格式读入K。把K转成千进制Kt,同时变为int型。
把数字往大进制转换能够加快运算效率。若用十进制则耗费很多时间,会TLE。
千进制的性质与十进制相似。
例如,把K=1234567890转成千进制,就变成了:Kt=[ 1][234][567][890]。
为了方便处理,我的程序是按“局部有序,全局倒序”模式存放Kt
即Kt=[890][567][234][1 ] (一个中括号代表一个数组元素)
2、 素数打表,把10^6内的素数全部预打表,在求模时则枚举到小于L为止。
注意打表不能只打到100W,要保证素数表中最大的素数必须大于10^6,否则当L=100W且K为GOOD时,会因为数组越界而RE,这是因为越界后prime都是负无穷的数,枚举的while(prime[pMin]<L)循环会陷入死循环
3、 高精度求模。
主要利用Kt数组和同余模定理。
例如要验证123是否被3整除,只需求模124%3
但当123是一个大数时,就不能直接求,只能通过同余模定理对大数“分块”间接求模
具体做法是:
先求1%3 = 1
再求(1*10+2)%3 = 0
再求 (0*10+4)% 3 = 1
那么就间接得到124%3=1,这是显然正确的
而且不难发现, (1*10+2)*10+4 = 124
这是在10进制下的做法,千进制也同理,*10改为*1000就可以了
#include <iostream>
#include<stdio.h>
#include<vector>
#include<string.h>
using namespace std;
int prime[2000000];
#define MAX 2000000
typedef struct BigInt
{
int theInt[10000];
int len;
}BigInt;
BigInt bigInt;
void primeTable()
{
long num;
num=0;
prime[num++]=2;
for(int i=3;i<2000000;i+=2)
{
int flag=true;
for(int j=0;prime[j]*prime[j]<=i;j++)
{
if(i%prime[j]==0){flag=false;break;}
}
if (flag)
{
prime[num++]=i;
}
}
}
void convert(char s[])
{
int lens=strlen(s);
bigInt.len=(lens+2)/3;
int ge,shi,bai,i,num=1;
for(i=lens-1;i>=2;i-=3)
{
ge=s[i]-'0';
shi=s[i-1]-'0';
bai=s[i-2]-'0';
bigInt.theInt[num++]=bai*100+shi*10+ge;
}
if (i==0)
{
ge=s[i]-'0';
bigInt.theInt[num++]=ge;return;
}
if (i==1)
{
ge=s[i]-'0';
shi=s[i-1]-'0';
bigInt.theInt[num++]=shi*10+ge;
}
}
bool divide(long number)
{
int yushu=0;
for (int i = bigInt.len; i >=1; i--)
{
yushu=(yushu*1000+bigInt.theInt[i])%number;
}
if (yushu==0)
{
return true;
}
return false;
}
int main()
{
primeTable();
char K[10000];long l;
while(true)
{
for(int i=0;i<10000;i++)K[i]=NULL;
cin>>K>>l;
if (strlen(K)==1&&K[0]=='0'&&l==0)
{
return 0;
}
convert(K);
bool flag=true;int i;
for(i=0;prime[i]<l;i++)
{
if (divide(prime[i])==true)
{
flag=false;
cout<<"BAD "<<prime[i]<<endl;
break;
}
}
if (flag)
{
cout<<"GOOD"<<endl;
}
}
}
相关文章推荐
- poj 2635 The Embarrassed Cryptographer 筛素数+高精度除法
- POJ 2635 The Embarrassed Cryptographer (大整数求模/高精度求模 + 同余模定理 +素数打表)
- POJ 2635-The Embarrassed Cryptographer(高精度求模+同余模定理)
- POJ 2635 The Embarrassed Cryptographer(素数线性筛法)
- POJ 2635 The Embarrassed Cryptographer [高精度求余+同余模定理]【数论】
- poj 2635(The Embarrassed Cryptographer(把…译成密码) 素数打表的最优方法+10进制转换成1000进制,大数取模
- poj 2635 The Embarrassed Cryptographer (素数筛选优化+同余定理)
- poj 2635 高精度取模
- poj 2635 素数打表+同余求模定理+千进制
- POJ-2635 The Embarrassed Cryptographer 万进制+素数筛选
- POJ 2635 高精度MOD 和 乱搞的进制转换
- poj 2635 大数模运算(内有打素数表的模板,大树求余分解公式)
- POJ 2635 The Embarrassed Cryptographer 线性筛+高精度取模
- poj 2635 The Embarrassed Cryptographer(素数筛 + 同余模定理)
- POJ 2635 The Embarrassed Cryptographer【数论,千进制,高精度求模+同余模定理】
- poj2635——The Embarrassed Cryptographer(高精度取模)
- [ACM] POJ 2635 The Embarrassed Cryptographer (同余定理,素数打表)
- POJ 2635 The Embarrassed Cryptographer 高精度
- The Embarrassed Cryptographer POJ 2635 数论之高精度求模(同余模定理+千进制)
- [ACM] POJ 2635 The Embarrassed Cryptographer (同余定理,素数打表)
